Business Operation Support Services (BOSS) Data Governance Operational Risk Management Compliance Security and Risk Management Presentation Services Information Services Infrastructure Services Facility Security Asset Handling Controlled Physical Access Information Technology Operation & Support (ITOS) Application Services Service Support Configuration Management Problem Management Incident Management Change Management Release Management Service Delivery Policies and Standards Data Protection Audit Planning Reference Architecture Version 2.0 Guiding Principles q Define protections that enable trust in the cloud. q Develop cross-platform capabilities and patterns for proprietary and open-source providers. q Will facilitate trusted and efficient access, administration and resiliency to the customer/consumer. q Provide direction to secure information that is protected by regulations. q The Architecture must facilitate proper and efficient identification, authentication, authorization, administration and auditability. q Centralize security policy, maintenance operation and oversight functions. q Access to information must be secure yet still easy to obtain. q Delegate or Federate access control where appropriate. q Must be easy to adopt and consume, supporting the design of security patterns q The Architecture must be elastic, flexible and resilient supporting multi-tenant, multi-landlord platforms q The architecture must address and support multiple levels of protection, including network, operating system, and application security needs. High Level Use Cases Co-Chairs: Jairo Orea, Yaron Levi, Dan Logan. Team: Richard Austin, Frank Simorjay, Yaron Levi, Jon-Michael Brook, Jarrod Stenberg, Ken Trant, Earle Humphreys, Vern Williams Date: 02/25/2013 SABSA ITIL v3 JERICHO Independent Audits Third-Party Audits Internal Audits Contact/Authority Maintenance Information System Regulatory Mapping Intellectual Property Protection Data Ownership / Stewardship Data Classification Handling / Labeling / Security Policy Secure Disposal of Data Data Governance Risk Assessments Non- Production Data Rules for Information Leakage Prevention Information Leakage Metadata Technical Security Standards Data/Asset Classification Barriers Electronic Surveillance Physical Authentication Security Patrols Business Impact Analysis TOGAF Data Software Hardware Information Technology Resiliency Capacity Planning Software Management Physical Inventory Automated Asset Discovery Configuration Management Emergency Changes Planned Changes Project Changes Scheduling Operational Chages Service Provisioning Approval Workflow Change Review Board Security Incident Response Automated Ticketing Self-Service Ticketing Event Classifiation Root Cause Analysis Source Code Management Trend Analysis Problem Resolution Testing Build Version Control Availability Management Resiliency Analysis Capacity Planning Service Level Management Objectives Internal SLAs External SLAs Vendor Management OLAs Service Dashboard Asset Management Service Costing Operational Bugdeting Investment Budgeting Charge Back Connectivity & Delivery Abstraction Integration Middleware Programming Interfaces Knowledge Management Presentation Modality Presentation Platform Service Support Configuration Rules (Metadata) Service Events Service Delivery Service Catalog SLAs OLAs Contracts Recovery Plans Business Continuity Domain Container Process or Solution Data Human Resources Security Crisis Management Background Screening Employment Agreements Employee Termination Governance Risk & Compliance Policy Management IT Risk Management Compliance Management Technical Awareness and Training InfoSec Management Capability Mapping Risk Portfolio Management Risk Dashboard Vendor Management Audit Management Residual Risk Management Best practices Trend Analysis Benchmarking Job Descriptions Roles and Responsibilities Employee Code of Conduct IT Operation Resource Management Segregation of Duties PMO Portfolio Management Maturity Model Roadmap IT Governance Architectrure Governance Standards and Guidelines Project Mgmnt Clear Desk Policy Strategy Alignment Data Loss Prevention Network (Data in Transit) End-Point (Data in Use) Server (Data at Rest) Intellectual Property Protection Intellectual Property Digital Rights Management Cryptographic Services Threat and Vulnerability Management Patch Management Compliance Testing Databases Signature Services PKI Data-in-Transit Encryption (Transitory, Fixed) Privilege Management Infrastructure Identity Management Domain Unique Identifier Federated IDM Identity Provisioning Attribute Provisioning Authentication Services SAML Token Risk Based Auth OTP Smart Card Multifactor Password Management Authorization Services Policy Enforcement Policy Definition Policy Mangement Principal Data Management Resource Data Management XACML Network Authentication Biometrics Single Sign On Middleware Authentication WS-Security Privilege Usage Management Servers Network Vulnerability Management Application Infrastructure DB Penetration Testing Internal External Threat Management Source Code Scanning Risk Taxonomy Infrastructure Protection Services Server Anti- Virus HIPS / HIDS Host Firewall End-Point Anti-Virus, Anti-Spam, Anti-Malware HIPS /HIDS Host Firewall Data-at-Rest Encryption (DB, File, SAN, Desktop, Mobile) Media Lockdown Hardware Based Trusted Assets Forensic Tools Inventory Control Content Filtering Application XML Applicance Application Firewall Secure Messaging Secure Collaboration Network Firewall Content Filtering NIPS / NIDS Link Layer Network Security Wireless Protection User Directory Services Active Directory Services LDAP Repositories X.500 Repositories DBMS Repositories Registry Services Location Services Federated Services Reporting Services Dashboard Reporting Tools Data Mining Business Intelligence Virtual Directory Services Security Monitoring Risk Management GRC RA BIA DR & BC Plans VRA TVM Availability Services Network Services Storage Services Development Process Configuration Management Database (CMDB) Knowledge Repository Change Logs Meta Directory Services Internal Infrastructure Servers End-Points Virtual Infrastructure BOSS SaaS, PaaS, IaaS Identity Verification DPI Session Events Authorization Events Authentication Events Application Events Network Events Computer Events Risk Assessments Audit Findings Data Classification Process Ownership HR Data (Employees & Contractors) Business Strategy HIPS Database Events ACLs CRLs Compliance Monitoring NIPS Events DLP EVents Transformation Services NIPS Events Privilege Usage Events eDiscovery Events ITOS PMO Strategy Problem Management Incident Management CMDB Knowledge Management Service Management Change Management Roadmap Security Monitoring Services SIEM Platform Event Mining Database Monitoring Application Monitoring End-Point Monitoring Event Correlation SOC Portal Market Threat Intelligence Counter Threat Management Cloud Monitoring Honey Pot E-Mail Journaling Managed Security Services Knowledge Base Branding Protection Anti-Phishing Legal Services Contracts E-Discovery Internal Investigations Forensic Analysis Data lifecycle management Data De-Identification Life cycle management Data Seeding Data Tagging Meta Data Control e-Mail Journaling Data Obscuring Data Masking eSignature (Unstructured data) Key Management Symmetric Keys Asymmetric Keys Role Management Keystroke/Session Logging Privilege Usage Gateway Password Vaulting Resource Protection DRP Plan Management Test Management Contractors Network External (VLAN) Internal (VNIC) Application Virtualization Desktop “Client” Virtualization Local Remote Session- Based VM-Based (VDI) Server Virtualization Virtual Machines (Hosted Based) Hardware-Assisted Paravirtualization Full Storage Virtualization <<insert Jairo’s content> Network Address Space Virtualization IPv4 IPv6 OS VIrtualization TPM Virtualization Server Application Streaming Block-Based Virtualization Host-Based Storage Device- Based Network-Based LVM LUN LDM Appliance Switched File-Based Virtualization Database Virtualization Virtual Memory Client Application Streaming Mobile Device Virtualization Smartcard Virtualization Virtual Workspaces Data Discovery Obligation Remediation Exceptions Self Assessment Program Mgmnt Best Practices & Regulatory correlation Image Management Out of the Box (OTB) AutZ Application Performance Monitoring Security Knowledge Lifecycle Security Design Patterns Real-time internetwork defense (SCAP) Cross Cloud Security Incident Response User Behavior & Profile Patterns Black Listing Filtering Self-Service Security Code Review Application Vulnerability Scanning Stress and Volume Testing Attack Patterns Real Time Filtering Software Quality Assurance Security Application Framwrok - ACEGI Code Samples Risk Management Framework Employee Awareness Security Job Aids Security FAQ Orphan Incident Management Secure Build Compliance Monitoring Service Discovery OTB AutN Mobile Devices Desktops Portable Devices Smart Appliances Medical Devices Handwriting (ICR) Speech Recognition (IVR) Company owned Third-Party Public Kiosk Consumer Service Platform Social Media Colaboration Enterprise Service Platform B2B B2C B2E B2M Search E-Mail P2P e-Readers Rules for Data Retention Information Security Policies Independent Risk Management Operational Security Baselines Job Aid Guidelines Role Based Awareness Business Assessment Technical Assessment Data-in-use Encryption (Memory) Incident Response Legal Preparation Key Risk Indicators Fixed Devices Mobile Device Management Equipment Maintenance Data Segregation Input Validation Planning Testing Environmental Risk Management Physical Security Equipment Location Power Redundancy Network Segmentation Authoritative Time Source White Listing White Listing Operational Risk Committee End Point Entitlement Review Sensitive File Protection Behavioral Malware Prevention Hypervisor Governance and Compliance Vertical Isolation Behavioral Malware Prevention Behavioral Malware Prevention Secure Sandbox

Welcome message from author
This document is posted to help you gain knowledge. Please leave a comment to let me know what you think about it! Share it to your friends and learn new things together.
Transcript
-
Business Operation
Support Services
(BOSS)
Data Governance
Operational Risk
Management
Compliance
Security and Risk
Management
Presentation Services
Information Services
Infrastructure Services
Facility Security
Asset
Handling
Controlled Physical
Access
Information Technology
Operation & Support
(ITOS)
Application Services
Service Support
Configuration Management
Problem ManagementIncident Management
Change Management Release
Management
Service Delivery
Policies and Standards
Data Protection
Audit Planning
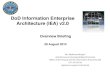
Reference Architecture Version 2.0
Guiding Principlesq Define protections that enable trust in the cloud.
q Develop cross-platform capabilities and patterns for proprietary and open-source providers.
q Will facilitate trusted and efficient access, administration and resiliency to the customer/consumer.
q Provide direction to secure information that is protected by regulations.
q The Architecture must facilitate proper and efficient identification, authentication, authorization, administration and auditability.
q Centralize security policy, maintenance operation and oversight functions.
q Access to information must be secure yet still easy to obtain.
q Delegate or Federate access control where appropriate.
q Must be easy to adopt and consume, supporting the design of security patterns
q The Architecture must be elastic, flexible and resilient supporting multi-tenant, multi-landlord platforms
q The architecture must address and support multiple levels of protection, including network, operating system, and application security needs.
High Level Use Cases
Co-Chairs: Jairo Orea, Yaron Levi, Dan Logan.
Team: Richard Austin, Frank Simorjay, Yaron Levi, Jon-Michael Brook,
Jarrod Stenberg, Ken Trant, Earle Humphreys, Vern Williams
Date: 02/25/2013
SABSA
ITIL v3
JERICHO
Independent
Audits
Third-Party
Audits
Internal
Audits
Contact/Authority
Maintenance
Information System Regulatory
MappingIntellectual Property Protection
Data Ownership /
Stewardship
Data
Classification
Handling / Labeling /
Security Policy
Secure Disposal of
Data
Data Governance
Risk
Assessments
Non-
Production
Data
Rules for Information
Leakage Prevention
Information
Leakage
Metadata
Technical Security
StandardsData/Asset Classification
BarriersElectronic
Surveillance
Physical
AuthenticationSecurity Patrols
Business
Impact Analysis
TOGAF
Data
SoftwareHardware
Information Technology
Resiliency
Capacity PlanningSoftware
ManagementPhysical Inventory
Automated Asset
Discovery
Configuration
Management
Emergency
Changes
Planned Changes
Project
Changes
Scheduling
Operational
Chages
Service
Provisioning
Approval
Workflow
Change
Review
Board
Security Incident
Response
Automated
Ticketing
Self-Service Ticketing
Event
Classifiation
Root Cause
Analysis
Source Code
Management
Trend
Analysis
Problem
Resolution
Testing
Build
Version
Control
Availability
Management
Resiliency
Analysis
Capacity Planning
Service Level
Management
Objectives Internal SLAs
External SLAs
Vendor Management
OLAs
Service Dashboard
Asset Management
Service
Costing
Operational
Bugdeting
Investment
Budgeting
Charge
Back
Connectivity & Delivery
Abstraction
Integration MiddlewareProgramming Interfaces
Knowledge Management
Presentation Modality
Presentation Platform
Service Support
Configuration
Rules
(Metadata)
Service
Events
Service DeliveryService
CatalogSLAs OLAs
ContractsRecovery
Plans
Business Continuity
DomainContainer
Process or
SolutionData
Human Resources
Security
Crisis
Management
Background
Screening
Employment
Agreements
Employee
Termination
Governance Risk &
CompliancePolicy Management
IT Risk
Management
Compliance
Management
Technical Awareness and Training
InfoSec
ManagementCapability
Mapping
Risk Portfolio
Management
Risk
Dashboard
Vendor
Management
Audit
Management
Residual Risk Management
Best
practices
Trend
AnalysisBenchmarking
Job
Descriptions
Roles and
Responsibilities
Employee Code of Conduct
IT Operation
Resource
Management
Segregation
of Duties
PMO Portfolio
Management
Maturity
Model
Roadmap
IT Governance
Architectrure
Governance
Standards and
Guidelines
Project
Mgmnt
Clear Desk Policy
Strategy Alignment
Data Loss Prevention
Network (Data in Transit)
End-Point(Data in Use)
Server(Data at Rest)
Intellectual Property
Protection
Intellectual
Property
Digital Rights
Management
Cryptographic Services
Threat and Vulnerability Management
Patch
Management
Compliance Testing
Databases
Signature
ServicesPKI
Data-in-Transit
Encryption (Transitory, Fixed)
Privilege Management Infrastructure
Identity ManagementDomain Unique
IdentifierFederated IDM
Identity
Provisioning
Attribute
Provisioning
Authentication ServicesSAML
Token
Risk Based
Auth
OTPSmart
Card
Multifactor
Password
Management
Authorization Services
Policy
EnforcementPolicy Definition
Policy
Mangement
Principal Data
Management
Resource Data
ManagementXACML
Network
Authentication
Biometrics
Single Sign OnMiddleware
AuthenticationWS-Security
Privilege Usage Management
Servers Network
Vulnerability Management
Application Infrastructure DB
Penetration Testing
Internal External
Threat ManagementSource Code Scanning Risk Taxonomy
Infrastructure Protection Services Server
Anti-
Virus
HIPS /
HIDS
Host
Firewall
End-PointAnti-Virus, Anti-Spam,
Anti-MalwareHIPS /HIDS
Host
Firewall
Data-at-Rest Encryption(DB, File, SAN, Desktop,
Mobile)
Media
Lockdown
Hardware Based
Trusted Assets
Forensic ToolsInventory Control
Content
Filtering
ApplicationXML Applicance Application Firewall
Secure Messaging Secure Collaboration
Network
Firewall Content
Filtering
NIPS /
NIDS
Link Layer Network Security
Wireless
Protection
User Directory Services
Active
Directory
Services
LDAP
Repositories
X.500
Repositories
DBMS
Repositories
Registry
Services
Location
Services
Federated
Services
Reporting Services
Dashboard Reporting ToolsData Mining Business Intelligence
Virtual
Directory
Services
Security Monitoring
Risk Management
GRC RA BIA
DR & BC
PlansVRA TVM
Availability
ServicesNetwork
Services
Storage
Services
Development Process
Configuration
Management
Database
(CMDB)
Knowledge
Repository
Change
Logs
Meta
Directory
Services
Internal Infrastructure
Servers
End-Points
Virtual Infrastructure
BOSS
SaaS,
PaaS, IaaS
Identity Verification
DPI
Session
Events
Authorization
Events
Authentication
EventsApplication
Events
Network
EventsComputer
Events
Risk
Assessments
Audit
Findings
Data
ClassificationProcess
Ownership
HR Data
(Employees &
Contractors)
Business
Strategy
HIPS
Database
Events
ACLs CRLs Compliance
Monitoring
NIPS
Events
DLP
EVents
Transformation Services
NIPS
Events
Privilege
Usage Events
eDiscovery
Events
ITOSPMO Strategy
Problem Management
Incident Management
CMDBKnowledge Management
ServiceManagement
ChangeManagement
Roadmap
Security Monitoring ServicesSIEM
Platform
Event
Mining
Database
Monitoring
Application
Monitoring
End-Point
Monitoring
Event
Correlation
SOC Portal
Market Threat
Intelligence Counter
Threat
Management
Cloud
Monitoring
Honey
Pot
E-Mail
Journaling
Managed Security
Services
Knowledge
Base
Branding
ProtectionAnti-Phishing
Legal ServicesContracts E-Discovery
Internal Investigations
Forensic
Analysis
Data lifecycle managementData
De-Identification
Life cycle
managementData Seeding
Data TaggingMeta Data
Control
e-Mail
Journaling
Data Obscuring
Data Masking
eSignature(Unstructured data)
Key ManagementSymmetric
Keys
Asymmetric
Keys
Role
Management
Keystroke/Session
Logging
Privilege Usage
Gateway
Password
Vaulting
Resource
Protection
DRP
Plan
Management
Test
Management
Contractors
Network
Virtualizaton
External
(VLAN)
Internal
(VNIC)
Application Virtualization
Desktop Client Virtualization
Local
Remote
Session-
Based
VM-Based
(VDI)
Server Virtualization
Virtual Machines (Hosted Based)
Hardware-AssistedParavirtualizationFull
Storage Virtualization
Related Documents