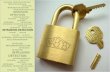
1 Systems Security ● Hardening of computer systems through 3 classes of protection mechanisms against adversaries – Prevention ● Physical world: Door/window locks, door security ● Computer security: Net/host firewalls, file permissions, reserved network ports, CPU ring security, vulnerability analysis/secure programming (SDLC) – Detection ● Physical world: Burglar alarm ● Computer security: Intrusion detection systems, anti-malware – Response (& Recovery) ● Physical world: Police investigation ● Computer security: Digital investigation/incident response, patching, attack surface reduction, attribution

Welcome message from author
This document is posted to help you gain knowledge. Please leave a comment to let me know what you think about it! Share it to your friends and learn new things together.
Transcript

1
Systems Security● Hardening of computer systems through 3 classes of protection
mechanisms against adversaries– Prevention
● Physical world: Door/window locks, door security● Computer security: Net/host firewalls, file permissions, reserved network ports, CPU ring
security, vulnerability analysis/secure programming (SDLC)
– Detection● Physical world: Burglar alarm● Computer security: Intrusion detection systems, antimalware
– Response (& Recovery)● Physical world: Police investigation● Computer security: Digital investigation/incident response, patching, attack surface
reduction, attribution

2
Access Control i
Subjects Securitycritical objectsin terms of: Confidentiality
Integrity Availability
Access ControlPolicy
Audit trail
● Predominantly preventive – ideal
– Authentication/Authorization/Audit
– Essential foundations for computer security
Enforcement
Configures
ControlledAccess
Authentication &Access Request
Log

3
Access Control ii● Security primitives
– Trusted computing bases (TCB) that enforce policies● Ring 0, Hypervisors, TEE, Sandboxes/Jails
– Cryptographic primitives● Stream/block ciphers● Public key crypto● Authentication/key exchange protocols● Authorization policies/Models for Access Control
– Machine learning● Classification/clustering of host/net logs
● No such thing as perfect security!

4
Broken Access Control i● Threats that bypass(type 1)/tamper (type 2) with protection mechanisms
● Predominantly detection/recovery mitigations
Subjects
Securitycritical objectsin terms of: Confidentiality
Integrity Availability
Access ControlPolicy
Audit trail
Enforcement
Type 2
Type 1
Configures
ControlledAccess
Authentication &Access Request
Log
Adversary

5
● Operating system– e.g. File permissions (DAC), System privileges (MAC)– Type 1: Trojan – Type 1: Browser exploit + malware installation– Type 1: Exploiting misconfiguration to edit setuid’ed scripts having root as owner– Type 2: Bruteforce supervisor password
● Enterprise application– e.g. restricted/privileged areas, accountcentric forms– Type 1: Password theft– Type 2: Exploit insufficient mechanism
● E.g. Discover a form button that takes to a sensitive application form without application referring request to access control mechanism
Broken Access Control ii

6
● Web portals– to enterprise applications– Type 1 – SQL injection attack– Type 2 – Exploit nonrandom session identifiers
● Network Firewall– DMZs, Wifi isolation– Type 1 – IP address spoofing– Type 2 – Malicious defragmentation attack
Broken Access Control iii

7
● Malicious logic: ultimate goals– System take over/pivoting– Complete access control subversion– Various forms and flavors
● Trojans● Exploits/drivebydownloads● Worms, Viruses● Scareware● Backdoors, Botnets● Spyware, Keyloggers● Ransomware● Launchers, Rootkits
Malware

8
● Static/dynamic binary code analysis/patching– Predominant security primitive for malware mitigation– Disassembly/reverse code engineering– Applications:
● Malware analysis, vulnerability analysis, inmemory patching, virtual machine introspection, memory forensics, exploit mitigation etc...
– Interactive malware analysis ideal place to start from– Identify malware goals and use output to configure security
tools e.g. IDS, memory dump analysis tools
Binary code analysis

9
Malware analysis i
● Dynamic disassembly

10
● Full knowledge of– Instruction trace, including dynamically linked libraries– CPU state– Execution flow state – stack– Data: global, heap, TLS
● However– Information overflow– Thousands of instructions and more– GBs of data– And despite of all this...
● Restricted to a single execution path
Malware analysis ii

11
● Iterative process, with each phase informing the next and refining a set of hypothesis about malware's goals
– Basic static analysis
Malware analysis iii
Using binary metadata> Architecture> Imports> Memory layout...
> Triage> Guidance for setting up sandbox probes> Static disassembly focus

12
Malware analysis iv
● Basic dynamic analysis: malware sandboxesHow about: Multiple execution paths? Evasive malware? Passwordprotected malware? Or just setting up the right environment e.g.> a keylogger but no Keystrokes are sent, or> IEtargeting spyware but no passwords storedin there, etc...
Need more context fromcode – Machine Code

13
Malware analysis v
● Static disassembly Gain: Control flow analysis API arguments Data structure analysis
But: Computed args may be hard to follow Optimized code/obscure idioms Packed code!
> Execution paths> Right environment> Follow areas of interest inside a debugger

14
Malware analysis vi
● Dynamic disassembly Directed analysis Infer obscure instructiontraces from memory/register values Patch! Unpack!
> Right environment setup> Patched/unpacked binary
> Goto: next iteration of analysis

15
Guide detection
alert tcp $HOME_NET 21 > $EXTERNAL_NET any (msg:"BLEEDINGEDGE SCANPotential FTP BruteForce attempt"; flow:from_server,established;content:"530 "; pcre:"/^530\s+(Login|User)/smi"; classtype:unsuccessfuluser; threshold: type threshold, track by_dst, count 5, seconds 120;sid:2002383; rev:3;)

16
Guide digital investigation

17
But first...
● Acquisition– Infected hosts– Suspicious network traffic
Related Documents