© L T T A O B © 2013 Cisco and Lab - Us Topology – Part 1 will Topology – Part 2 will console c Addressing S PC Objectives Part 1: Id Part 2: Id Backgroun The two p 768. Both transport provides t Note: Und engineers d/or its affiliates. sing Wir – Part 1 (FT l highlight a T – Part 2 (TF l highlight a U onnection to g Table (Pa Device 1 V C-A N entify TCP H entify UDP H nd / Scenar protocols in th protocols su layer support transport laye derstanding th s. All rights reserve eshark t TP) TCP capture o FTP) UDP capture o Switch S1. art 2) Interface VLAN 1 NIC Header Fields Header Fields rio he TCP/IP tran pport upper-la t for the Hype er support for he parts of th ed. This docume to Exam of an FTP ses of a TFTP ses IP Ad 192.168 192.168 s and Operat s and Operat nsport layer a ayer protocol erText Transfe the Domain N e TCP and U ent is Cisco Publi mine FTP ssion. This top ssion. The PC ddress S 8.1.1 25 8.1.3 25 tion Using a tion Using a are the TCP, d communicat er Protocol (H Name System DP headers a ic. P and TF pology consis C must have b Subnet Mask 55.255.255.0 55.255.255.0 Wireshark F Wireshark T defined in RF ion. For exam HTTP) and FT m (DNS) and T and operation FTP Cap sts of a PC wi both an Ether k Default 0 N/A 0 192.168 FTP Session TFTP Sessio FC 761, and U mple, TCP is u TP protocols, TFTP among n are a critica P ptures ith Internet ac rnet connectio t Gateway 8.1.1 Capture n Capture UDP, defined used to provid among others others. al skill for netw Page 1 of 14 ccess. on and a in RFC de s. UDP work

Welcome message from author
This document is posted to help you gain knowledge. Please leave a comment to let me know what you think about it! Share it to your friends and learn new things together.
Transcript

©
L
T
T
A
O
B
© 2013 Cisco and
Lab - Us
Topology –
Part 1 will
Topology –
Part 2 willconsole c
Addressing
S
PC
Objectives
Part 1: Id
Part 2: Id
Backgroun
The two p768. Bothtransport provides t
Note: Undengineers
d/or its affiliates.
sing Wir
– Part 1 (FT
l highlight a T
– Part 2 (TF
l highlight a Uonnection to
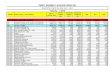
g Table (Pa
Device
1 V
C-A N
entify TCP H
entify UDP H
nd / Scenar
protocols in th protocols sulayer supporttransport laye
derstanding ths.
All rights reserve
eshark t
TP)
TCP capture o
FTP)
UDP capture oSwitch S1.
art 2)
Interface
VLAN 1
NIC
Header Fields
Header Fields
rio
he TCP/IP tranpport upper-lat for the Hypeer support for
he parts of th
ed. This docume
to Exam
of an FTP ses
of a TFTP ses
IP Ad
192.168
192.168
s and Operat
s and Operat
nsport layer aayer protocol
erText Transfethe Domain N
e TCP and U
ent is Cisco Publi
mine FTP
ssion. This top
ssion. The PC
ddress S
8.1.1 25
8.1.3 25
tion Using a
tion Using a
are the TCP, dcommunicat
er Protocol (HName System
DP headers a
ic.
P and TF
pology consis
C must have b
Subnet Mask
55.255.255.0
55.255.255.0
Wireshark F
Wireshark T
defined in RFion. For exam
HTTP) and FTm (DNS) and T
and operation
FTP Cap
sts of a PC wi
both an Ether
k Default
0 N/A
0 192.168
FTP Session
TFTP Sessio
FC 761, and Umple, TCP is uTP protocols, TFTP among
n are a critica
P
ptures
ith Internet ac
rnet connectio
t Gateway
8.1.1
Capture
n Capture
UDP, defined used to providamong others others.
al skill for netw
Page 1 of 14
ccess.
on and a
in RFC de s. UDP
work

Lab - Using Wireshark to Examine FTP and TFTP Captures
© 2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 2 of 14
In Part 1 of this lab, you will use Wireshark open source tool to capture and analyze TCP protocol header fields for FTP file transfers between the host computer and an anonymous FTP server. The Windows command line utility is used to connect to an anonymous FTP server and download a file. In Part 2 of this lab, you will use Wireshark to capture and analyze UDP protocol header fields for TFTP file transfers between the host computer and Switch S1.
Note: The switch used is a Cisco Catalyst 2960s with Cisco IOS Release 15.0(2) (lanbasek9 image). Other switches and Cisco IOS versions can be used. Depending on the model and Cisco IOS version, the available commands and output produced might vary from what displays in the labs.
Note: Make sure that the switch has been erased and has no startup configurations. If you are unsure, contact your instructor.
Note: Part 1 assumes the PC has Internet access and cannot be performed using Netlab. Part 2 is Netlab compatible.
Required Resources – Part 1 (FTP)
1 PC (Windows 7, Vista, or XP with command prompt access, Internet access, and Wireshark installed)
Required Resources – Part 2 (TFTP)
1 Switch (Cisco 2960 with Cisco IOS Release 15.0(2) lanbasek9 image or comparable)
1 PC (Windows 7, Vista, or XP with Wireshark and a TFTP server, such as tftpd32 installed)
Console cable to configure the Cisco IOS devices via the console port
Ethernet cable as shown in the topology
Part 1: Identify TCP Header Fields and Operation Using a Wireshark FTP Session Capture
In Part 1, you use Wireshark to capture an FTP session and inspect TCP header fields.
Step 1: Start a Wireshark capture.
a. Close all unnecessary network traffic, such as the web browser, to limit the amount traffic during the Wireshark capture.
b. Start the Wireshark capture.
Step 2: Download the Readme file.
a. From the command prompt, enter ftp ftp.cdc.gov.
b. Log into the FTP site for Centers for Disease Control and Prevention (CDC) with user anonymous and no password.
c. Locate and download the Readme file.

L
©
S
S
Lab - Using W
© 2013 Cisco and
Step 3: Sto
Step 4: Vie
Wiresharkanalysis, t198.246.1
Wireshark to
d/or its affiliates.
op the Wire
ew the Wire
k captured matype tcp and 112.54, is the
Examine FT
All rights reserve
shark captu
eshark Main
any packets dip.addr == 1address for f
TP and TFTP
ed. This docume
ure.
n Window.
during the FT98.246.112.5
ftp.cdc.gov.
Captures
ent is Cisco Publi
P session to f54 in the Filte
ic.
ftp.cdc.gov. Ter: entry area
To limit the ama and click Ap
P
mount of datapply. The IP a
Page 3 of 14
a for address,

L
©
S
Lab - Using W
© 2013 Cisco and
Step 5: An
After the Ttransport illustrates
TCP is rowindow siAt the conTCP perfo
In Wireshfirst TCP dappears s
The image
Wireshark to
d/or its affiliates.
nalyze the T
TCP filter haslayer protocothe three-wa
utinely used dize. For each nclusion of theorms an orde
ark, detailed datagram fromsimilar to the p
e above is a T
Examine FT
All rights reserve
CP fields.
s been appliedol TCP creatinay handshake
during a sessdata exchang
e data transferly shutdown
TCP informatm the host copacket detail
TCP datagram
TP and TFTP
ed. This docume
d, the first thrng a reliable se.
ion to controlge between ter, the TCP seand terminat
tion is availabomputer, andpane shown
m diagram. A
Captures
ent is Cisco Publi
ree frames in ession. The s
datagram dehe FTP clientession is closion.
ble in the packexpand the Tbelow.
An explanation
ic.
the packet lissequence of [
elivery, verify t and FTP sersed. Finally, w
ket details paTCP record. T
n of each field
st pane (top s[SYN], [SYN,
datagram arrrver, a new T
when the FTP
ane (middle seThe expanded
d is provided f
P
section) displaACK], and [A
rival, and manTCP session isP session is fin
ection). Highld TCP datagra
for reference
Page 4 of 14
ays the ACK]
nage s started. nished,
ight the am
:

Lab - Using Wireshark to Examine FTP and TFTP Captures
© 2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 5 of 14
The TCP source port number belongs to the TCP session host that opened a connection. The value is normally a random value above 1,023.
The TCP destination port number is used to identify the upper layer protocol or application on the remote site. The values in the range 0–1,023 represent the “well-known ports” and are associated with popular services and applications (as described in RFC 1700, such as Telnet, FTP, HTTP, and so on). The combination of the source IP address, source port, destination IP address, and destination port uniquely identifies the session to both sender and receiver.
Note: In the Wireshark capture below, the destination port is 21, which is FTP. FTP servers listen on port 21 for FTP client connections.
The Sequence number specifies the number of the last octet in a segment.
The Acknowledgment number specifies the next octet expected by the receiver.
The Code bits have a special meaning in session management and in the treatment of segments. Among interesting values are:
- ACK — Acknowledgement of a segment receipt.
- SYN — Synchronize, only set when a new TCP session is negotiated during the TCP three-way handshake.
- FIN — Finish, request to close the TCP session.
The Window size is the value of the sliding window; determines how many octets can be sent before waiting for an acknowledgement.
The Urgent pointer is only used with an Urgent (URG) flag when the sender needs to send urgent data to the receiver.
The Options has only one option currently, and it is defined as the maximum TCP segment size (optional value).
Using the Wireshark capture of the first TCP session startup (SYN bit set to 1), fill in information about the TCP header:
From the PC to CDC server (only the SYN bit is set to 1):
Source IP Address:
Destination IP Address:
Source port number:
Destination port number:
Sequence number:
Acknowledgement number:
Header length:
Window size:
In the second Wireshark filtered capture, the CDC FTP server acknowledges the request from the PC. Note the values of the SYN and ACK bits.

L
©
Lab - Using W
© 2013 Cisco and
Fill in the
Sour
Dest
Sour
Dest
Sequ
Ackn
Hea
Wind
In the finamessage to 1.
Wireshark to
d/or its affiliates.
following info
rce IP addres
tination IP ad
rce port numb
tination port n
uence numbe
nowledgemen
der length:
dow size:
al stage of theto the server
Examine FT
All rights reserve
ormation rega
ss:
dress:
ber:
number:
er:
nt number:
e negotiation t. Notice only
TP and TFTP
ed. This docume
rding the SYN
to establish cthe ACK bit is
Captures
ent is Cisco Publi
N-ACK messa
ommunicatios set to 1, and
ic.
age.
ns, the PC sed the Sequen
ends an acknonce number ha
P
owledgementas been incre
Page 6 of 14
t emented

L
©
Lab - Using W
© 2013 Cisco and
Fill in the
Sour
Dest
Sour
Dest
Sequ
Ackn
Head
Wind
How man
After a TCserver comWhen theacknowled
Wireshark to
d/or its affiliates.
following info
rce IP addres
tination IP ad
rce port numb
tination port n
uence numbe
nowledgemen
der length:
dow size:
y other TCP d
CP session is mmunicate be
e FTP server sdgment to the
Examine FT
All rights reserve
ormation rega
ss:
dress:
ber:
number:
er:
nt number:
datagrams co
established, etween each sends a Respe TCP sessio
TP and TFTP
ed. This docume
rding the ACK
ontained a SY
FTP traffic caother, unawa
ponse: 220 to n on the serv
Captures
ent is Cisco Publi
K message.
YN bit?
an occur betware that TCP h
the FTP clienver. This sequ
ic.
ween the PC ahas control annt, the TCP s
uence is visibl
and FTP servnd managem
session on thele in the Wire
P
ver. The FTP ent over the s
e FTP client sshark capture
Page 7 of 14
client and session. sends an e below.

L
©
Lab - Using W
© 2013 Cisco and
When theacknowledsends a Tsession aWhen theis sent to and captu
By applyinsequencefile. After
Wireshark to
d/or its affiliates.
e FTP sessiondges the FTP
TCP datagramcknowledges
e originator of acknowledge
ure below.
ng an ftp filtee of the eventsthe file transf
Examine FT
All rights reserve
n has finishedP termination wm to the FTP c receipt of thethe TCP term
e the terminat
r, the entire ss during this Ffer completed
TP and TFTP
ed. This docume
, the FTP cliewith a Respoclient, announe termination mination, FTPion and the T
sequence of thFTP session. , the user end
Captures
ent is Cisco Publi
ent sends a coonse: 221 Gooncing the termdatagram, th server, recei
TCP session is
he FTP trafficThe usernam
ded the FTP s
ic.
ommand to “qodbye. At thismination of thehen sends its ives a duplicas closed. This
c can be examme anonymousession.
quit”. The FTPs time, the FTe TCP sessioown TCP ses
ate terminatios sequence is
mined in Wireus was used t
P
P server TP server TCPon. The FTP cssion terminaton, an ACK das visible in the
eshark. Noticeto retrieve the
Page 8 of 14
P session client TCP tion. atagram e diagram
e the e Readme

L
©
P
S
Lab - Using W
© 2013 Cisco and
Apply the transmittemust term
In this exaset in framthe server
In frame 6with an ACFTP serve
Part 2: IdS
In Part 2,
Step 1: Se
a. Estab
b. If not the de
Wireshark to
d/or its affiliates.
TCP filter aged for the termminate indepe
ample, the FTme 63. The PCr to the client
65, the PC seCK to acknower and PC.
dentify USession C
you use Wire
t up this ph
blish a console
already doneefault gatewa
Examine FT
All rights reserve
ain in Wireshmination of thendently. Exam
TP server hasC sends an Ain frame 64.
ends a FIN to wledge the FIN
DP HeadCapture
eshark to capt
hysical topo
e and Etherne
e, manually coy.
TP and TFTP
ed. This docume
hark to examine TCP sessiomine the sour
s no more datACK to acknow
the FTP servN from the PC
er Fields
ture a TFTP s
ology and p
et connection
onfigure the IP
Captures
ent is Cisco Publi
ne the terminaon. Because Trce and destin
a to send in twledge the re
ver to terminatC in frame 67
s and Ope
session and i
repare for T
n between PC
P address on
ic.
ation of the TTCP connectionation addres
the stream; it eceipt of the F
te the TCP se7. Now the TC
eration Us
nspect UDP h
TFTP captu
C-A and Switc
the PC to 19
TCP session. on is full-dupl
sses.
sends a segmFIN to termina
ession. The FCP session te
sing a W
header fields
re.
ch S1.
92.168.1.3. It
P
Four packetslex, each dire
ment with theate the sessio
FTP server resrminated betw
Wireshark
.
is not require
Page 9 of 14
s are ection
FIN flag on from
sponds ween the
TFTP
ed to set

L
©
Lab - Using W
© 2013 Cisco and
c. Configpingin
Switc
Switc
EnterSwitc
S1(co
S1(co
S1(co
*Mar
*Mar changS1(co
S1# p
Type
Sendi
!!!!!
Succe
Wireshark to
d/or its affiliates.
gure the switcng 192.168.1.
ch> enable
ch# conf t
r configurch(config)
onfig)# in
onfig-if)#
onfig-if)#
1 00:37:
1 00:37:ged state onfig-if)#
ping 192.1
escape se
ing 5, 100
!
ess rate i
Examine FT
All rights reserve
ch. Assign an3. Troublesho
e
t
ration comm# host S1
nterface vl
# ip addres
# no shut
:50.166: %L
:50.175: %Lto up # end
168.1.3
equence to
0-byte ICMP
is 100 perc
TP and TFTP
ed. This docume
n IP address ooot as necess
mands, one
lan 1
ss 192.168
LINK-3-UPD
LINEPROTO-
abort.
P Echos to
cent (5/5)
Captures
ent is Cisco Publi
of 192.168.1.1sary.
e per line.
8.1.1 255.2
DOWN: Inter
-5-UPDOWN:
o 192.168.1
, round-tr
ic.
1 to VLAN 1.
. End wit
255.255.0
rface Vlan
Line prot
1.3, timeo
rip min/av
Verify conne
th CNTL/Z.
n1, changed
tocol on In
out is 2 se
vg/max = 1/
Pa
ctivity with the
d state to
nterface V
econds:
/203/1007
age 10 of 14
e PC by
o up
Vlan1,
ms

L
©
S
S
Lab - Using W
© 2013 Cisco and
Step 2: Pre
a. If it dobe co
b. Start t
c. Click your u
The T
Notice192.1
d. Test t
S1# c
Addre
Desti
!!
1638
If younot, thcheckusern
Step 3: Ca
a. OpenScrollApply
Wireshark to
d/or its affiliates.
epare the T
oes not alreadpied to this lo
tftpd32 on th
Browse and username.
TFTP server s
e that in Curre68.1.3.
the ability to c
copy start
ess or nam
ination fi
bytes cop
see that the hen troubleshk to make surname has ade
apture a TFT
Wireshark. Fl down and sey. Then click
Examine FT
All rights reserve
FTP server
dy exist, creatocation.
e PC.
change the c
should look lik
ent Directory,
copy a file usi
t tftp
me of remot
ilename [s1
pied in 0.0
file has copiehoot. If you gee your firewa
equate permis
TP session
From the Editelect UDP. ClOK.
TP and TFTP
ed. This docume
on the PC.
te a folder on
current directo
ke this:
, it lists the us
ng TFTP from
te host []
1-confg]?
026 secs (
ed (as in the aet the %Errorll is not block
ssion, such as
in Wireshar
t menu, choosick the Valida
Captures
ent is Cisco Publi
n the PC desk
ory to C:\Use
ser and the Se
m the switch t
? 192.168.
(63000 byte
above output)r opening ting TFTP, ans the desktop
rk
se Preferencate the UDP
ic.
ktop called TF
rs\user1\Des
erver (PC-A)
to the PC. Tro
.1.3
es/sec)
), then you aretftp (Permd that you are
p.
ces and click tchecksum if
FTP. The files
sktop\TFTP b
interface as t
oubleshoot as
e ready to gomission dene copying to a
the (+) sign tof possible ch
Pa
s from the swi
by replacing u
the IP addres
s necessary.
o on to the nexnied) error, a location wh
o expand Proheck box and
age 11 of 14
tch will
user1 with
ss of
xt step. If first ere your
otocols. click

L
©
Lab - Using W
© 2013 Cisco and
b. Start
c. Run t
d. Stop t
e. Set thused
In Wirfirst Umay bexpan
The fidatagport.
Wireshark to
d/or its affiliates.
a Wireshark c
he copy sta
the Wireshark
he filter to tftpto analyze tra
reshark, detaUDP datagrambe necessary nd box. The e
gure below isgram. Similar t
Examine FT
All rights reserve
capture.
art tftp co
k capture.
p. Your outputansport layer
iled UDP infom from the hos
to adjust the expanded UD
s a UDP datagto TCP, each
TP and TFTP
ed. This docume
ommand on th
t should look UDP operatio
ormation is avst computer, packet detailP datagram s
gram diagram UDP datagra
Captures
ent is Cisco Publi
he switch.
similar to theons.
ailable in the and move thels pane and eshould look si
m. Header infoam is identifie
ic.
e output show
Wireshark pae mouse poinexpand the UDmilar to the d
ormation is sped by the UDP
wn above. This
acket details nter to the pacDP record by
diagram below
parse, compaP source port
Pa
s TFTP transf
pane. Highligcket details pay clicking the pw.
ared to the TCt and UDP de
age 12 of 14
fer is
ght the ane. It protocol
CP estination

L
©
Lab - Using W
© 2013 Cisco and
Usingcheck
Sour
Dest
Sour
Dest
UDP
UDP
How d
Exam
Sour
Dest
Sour
Dest
UDP
UDP
Noticeremaiused
Also nYou c
Wireshark to
d/or its affiliates.
g the Wireshaksum value is
rce IP Addres
tination IP Ad
rce Port Num
tination Port N
P Message Le
P Checksum:
does UDP ve
mine the first fr
rce IP Addres
tination IP Ad
rce Port Num
tination Port N
P Message Le
P Checksum:
e that the retuinder of the Tto begin the T
notice that thecan learn mor
Examine FT
All rights reserve
rk capture of a hexadecim
ss:
ddress:
mber:
Number:
ength:
rify datagram
rame returned
ss:
ddress:
mber:
Number:
ength:
urn UDP dataFTP transfer.TFTP session
e UDP Checkre about why t
TP and TFTP
ed. This docume
the first UDPmal (base 16)
m integrity?
d from tftpd se
agram has a d. Because then is used to m
ksum is incorrthis happens
Captures
ent is Cisco Publi
P datagram, filvalue, denote
erver. Fill in t
different UDP ere is no relia
maintain the T
rect. This is mby searching
ic.
ll in informatioed by the prec
he informatio
source port, ble connectioFTP transfer.
most likely caug for “UDP che
on about the ceding 0x cod
on about the U
but this sourcon, only the or.
used by UDP ecksum offloa
Pa
UDP header.de:
UDP header:
ce port is useriginal source
checksum ofad”.
age 13 of 14
The
ed for the e port
ffload.

Lab - Using Wireshark to Examine FTP and TFTP Captures
© 2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 14 of 14
Reflection
This lab provided the opportunity to analyze TCP and UDP protocol operations from captured FTP and TFTP sessions. How does TCP manage communication differently than UDP?
Challenge
Because neither FTP nor TFTP are secure protocols, all transferred data is sent in clear text. This includes any user IDs, passwords, or clear-text file contents. Analyzing the upper-layer FTP session will quickly identify the user ID, password, and configuration file passwords. Upper-layer TFTP data examination is a bit more complicated, but the data field can be examined and the configuration user ID and password information extracted.
Cleanup
Unless directed otherwise by your instructor:
1) Remove the files that were copied to your PC.
2) Erase the configurations on switch S1.
3) Remove the manual IP address from the PC and restore Internet connectivity.
Related Documents