This topic is about how to use HERMESJMS over SSL enabled MQ Channel – (no MA setup). By Seri Charoensri 22 July 2012 ([email protected]) With IBM MQ Provider: If you experience error below with JSSE, certification not found. com.ibm.mq.MQException: JMSCMQ0001: WebSphere MQ call failed with compcode '2' ('MQCC_FAILED') reason '2397' ('MQRC_JSSE_ERROR'). at com.ibm.msg.client.wmq.common.internal.Reason.createException(Reason.java:223) at com.ibm.msg.client.wmq.internal.WMQConnection.<init>(WMQConnection.java:421) at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createV7ProviderConnection(WMQConnection Factory.java:6807) at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createProviderConnection(WMQConnectionFa ctory.java:6204) at com.ibm.msg.client.jms.admin.JmsConnectionFactoryImpl.createConnection(JmsConnectionFactoryImp l.java:278) at com.ibm.mq.jms.MQConnectionFactory.createCommonConnection(MQConnectionFactory.java:6155) 1. Hermes runs on standard JDK, with that Hermes is using JSSE security – cacerts (CA certificates store). Below we imported self-sign cert generated and extracted from IKEYMAN. IKEYMAN

Hermes jms ibmmq-ssl-channel-release2-with-mutual-authen
Nov 18, 2014
How to use Hemes with IBM MQ over SSL channel.
Welcome message from author
This document is posted to help you gain knowledge. Please leave a comment to let me know what you think about it! Share it to your friends and learn new things together.
Transcript

This topic is about how to use HERMESJMS over SSL enabled MQ Channel – (no MA setup).
By Seri Charoensri 22 July 2012 ([email protected])
With IBM MQ Provider: If you experience error below with JSSE, certification not found.
com.ibm.mq.MQException: JMSCMQ0001: WebSphere MQ call failed with compcode '2' ('MQCC_FAILED') reason '2397' ('MQRC_JSSE_ERROR').at com.ibm.msg.client.wmq.common.internal.Reason.createException(Reason.java:223)at com.ibm.msg.client.wmq.internal.WMQConnection.<init>(WMQConnection.java:421)at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createV7ProviderConnection(WMQConnectionFactory.java:6807)at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createProviderConnection(WMQConnectionFactory.java:6204)at com.ibm.msg.client.jms.admin.JmsConnectionFactoryImpl.createConnection(JmsConnectionFactoryImpl.java:278)at com.ibm.mq.jms.MQConnectionFactory.createCommonConnection(MQConnectionFactory.java:6155)
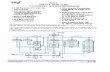
1. Hermes runs on standard JDK, with that Hermes is using JSSE security – cacerts (CA certificates store). Below we imported self-sign cert generated and extracted from IKEYMAN.
IKEYMAN

-----BEGIN CERTIFICATE-----
MIIBsTCCARqgAwIBAgIIqwony8vuHkgwDQYJKoZIhvcNAQEEBQAwGzELMAkGA1UEBhMCVVMxDDAK
BgNVBAMTA3FtNTAeFw0xMjA3MjAxMTE0NTlaFw0xMzA3MjExMTE0NTlaMBsxCzAJBgNVBAYTAlVT
MQwwCgYDVQQDEwNxbTUwgZ8wDQYJKoZIhvcNAQEBBQADgY0AMIGJAoGBAKH8o5PLJiJMKfihusFQ
7Y1XI3B/EuBIQZaBvQtF6fUVwmleedGBscc7v8Zac8P3AO6uQgv1INaZkQlKd4kDwzAG54wna4Jv
S4PS47dOBlixSL0FGufILK63/utyshwfGY4vsEuToEjhL5DAgMqmMpZIUMu8UilV3wRNYDQ8w5bH
AgMBAAEwDQYJKoZIhvcNAQEEBQADgYEAka8Fpec2GfS6dukxphyLe0jLWlbqrUdnMiRVmvcTIhM9
ukplpzDWUJ/f7Kof6cizSxYgvVjKYD2f4fEfgKHPU8hs/4UO0czdOM6cPobLOU6k5I9zN8o4eFqm
V/iuPyhswriJG1gQH4f0dA1HL0Ruv9kbvt0m46qroYXU5Ka6slc=
-----END CERTIFICATE-----
HermesJMS JVM

C:\Program Files (x86)\Java\jdk1.6.0_13\jre\lib\security\cacerts (I just use the default/provide truststore by JDK, you can use your truststore, if you like). Hermes will check the MQ Server’s cert from this trustore.
Keytool
2. For self-sign cert from MQ, you will need to import the cert into cacerts keystore, so that HERMES can hand-shake with MQ over SSL.
C:\Program Files (x86)\Java\jdk1.6.0_13\jre\bin>keytool -import -trustcacerts -alias qm5 -file ..\lib\security\QM12345-cert\QM5_cert.arm -keystore ..\lib\security\cacerts
Enter keystore password: changeit (default JSSE CA keystore)Owner: CN=qm5, C=USIssuer: CN=qm5, C=USSerial number: -54f5d8343411e1b8Valid from: Fri Jul 20 21:14:59 EST 2012 until: Sun Jul 21 21:14:59 EST 2013Certificate fingerprints: MD5: 7A:2C:20:3A:CE:94:2B:44:F0:C4:65:C8:FD:A4:17:9F SHA1: B5:D0:68:84:75:D2:6D:ED:61:AC:C6:32:87:F5:0C:69:28:AC:C0:6E Signature algorithm name: MD5withRSA Version: 3Trust this certificate? [no]: yCertificate was added to keystore
C:\Program Files (x86)\Java\jdk1.6.0_13\jre\bin>
HERMES JMS setting
IBM MQ 7 Provider Lib: - don’t need all of those lib – I am lazy to pick just the jars required.

C:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\com.ibm.mq.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\com.ibm.mq.jms.Nojndi.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\com.ibm.mq.soap.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\com.ibm.mqjms.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\commonservices.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\connector.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\dhbcore.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\fscontext.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\jms.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\jndi.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\jta.jarC:\Program Files (x86)\IBM\WebSphere MQ\Java\lib\ldap.jar
SSLCipherSuite SSL_RSA_WITH_3DES_EDE_CBC_SHAchannel qm5_ch1hostName 127.0.0.1port 1418queueManager QM5transportType 1
IBM MQ setup
On the MQ we have “TRIPLE_DES_SHA_SA” SSL setup – no client SSL (SSLCAUTH) required. “Authentication of Parties initiating connections: - Optional”. In short, we trust the MQ server’s SSL cert only, no Mutual Authentication setup for now. I will show you how to do MA below.

NOTE: we have not set the SSLCAUTH to be required, or lock down the DN name specification to only allow clients with the DN name come through.
Test result
We success fully retrieve data over SSL-enabled channel.

This topic is about how to use HERMESJMS over SSL enabled MQ Channel – (with MA setup).
With MA, the client (HERMESJMS in this case) will need to provide Client’s SSL to MQ server for Client Auth (SSLCAUTH-Required)
Setup a new SVRCONN channel for MA with DN spec.

Need to create Client’s Keystore - hermesclientkey.jks
NOTE: we use the default JDK truststore – cacerts to hold MQ SSL Cert (above). Alternatively, you could create your TrustStore and manage MQ Cert separately.
We will need create Hermes keystore since no default provided.
default keystore
No default. * javax.net.ssl.keyStore system propertyNote that the value NONE may be specified. This setting is appropriate if the keystore is not file-based (for example, it resides in a hardware token).
default keystore password
No default. * javax.net.ssl.keyStorePassword system property
default keystore provider
No default. * javax.net.ssl.keyStoreProvider system property
default keystore type
KeyStore.getDefaultType() * javax.net.ssl.keyStoreType system property
default truststore
jssecacerts, if it exists. Otherwise, cacerts
* javax.net.ssl.trustStore system property
default truststore password
No default. * javax.net.ssl.trustStorePassword system property

default truststore provider
No default. * javax.net.ssl.trustStoreProvider system property
default truststore type
KeyStore.getDefaultType() * javax.net.ssl.trustSt
Extract and Import our new Client Self-signed certs to MQ’s Keystore (CMS/KDB), so that MQ can trust our new client cert (this is self-sign, not signed by well-known CA certs that come with the default keystore)
HERMESJMS SETUP TO use the new personal keystore
The HERMESJMSkeystore.jks holds its certificate which will be exchange (MA) with the MQ server. Since this is a self-sign, we have given the key to MQ servers’s keystore (CMS KDB)
javax.net.ssl.keyStore = “C:/seri/HermesJMS/hermes client key/HERMESJMSkeystore.jks”
javax.net.ssl.keyStorePassword = “MySecretSorry”
We will use Default SunJSSE provider!! – you can use IBM or BouncyCastle, etc if you like if you need higher cipher e.g AES128. If you do so, don’t for get to add the Security Provider jars to

C:\Program Files (x86)\Java\jdk1.6.0_13\jre\lib\ext then “Add” the new security.provider to the java.secuirty file.
#java.security provider
# List of providers and their preference orders (see above):
#
security.provider.1=sun.security.provider.Sun
security.provider.2=sun.security.rsa.SunRsaSign
security.provider.3=com.sun.net.ssl.internal.ssl.Provider
security.provider.4=com.sun.crypto.provider.SunJCE
security.provider.5=sun.security.jgss.SunProvider
security.provider.6=com.sun.security.sasl.Provider
security.provider.7=org.jcp.xml.dsig.internal.dom.XMLDSigRI
security.provider.8=sun.security.smartcardio.SunPCSC
security.provider.9=sun.security.mscapi.SunMSCAPI
Syntax:
% java -Djavax.net.ssl.keyStore=keystore \ -Djavax.net.ssl.keyStorePassword=password Server
% java -Djavax.net.ssl.trustStore=truststore \ -Djavax.net.ssl.trustStorePassword=trustword Client
Example
C:\seri\HermesJMS\bin\Hermes.bat
start "HermesJMS" "%JAVA_HOME%\bin\javaw" -XX:NewSize=256m -Xmx1024m
-Djavax.net.ssl.keyStore="C:\seri\HermesJMS\hermes client key\hermesclientkey.jks"
-Djavax.net.ssl.keyStorePassword="secretPWD!"
-Djavax.net.debug="ssl,keymanager"
-Dhermes.home="%HERMES_HOME%" %HERMES_OPTS%
-Dlog4j.configuration="file:%HERMES_HOME%\bin\log4j.props"
-Dsun.java2d.noddraw=true
-Dhermes="%HERMES_CONFIG%\hermes-config.xml"
-Dhermes.libs="%HERMES_LIBS%" hermes.browser.HermesBrowser
NOTE: again, I simply leverage JDK’s truststore “cacerts” in ..\lib\security\

NOTE: HermesJMS will now start with the keystore hermesclientkey.jks for it to authenticate itself to MQ Server.
Test result with MA – no SSLPeer restriction
With MQ Sever’s SSLPeer restriction:

Hermes will fail since our CN is NOT “aa” – but cn=hermesclientkey

com.ibm.mq.MQException: JMSCMQ0001: WebSphere MQ call failed with compcode '2' ('MQCC_FAILED') reason '2059' ('MQRC_Q_MGR_NOT_AVAILABLE').
at com.ibm.msg.client.wmq.common.internal.Reason.createException(Reason.java:223)
at com.ibm.msg.client.wmq.internal.WMQConnection.<init>(WMQConnection.java:421)
at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createV7ProviderConnection(WMQConnectionFactory.java:6807)
at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createProviderConnection(WMQConnectionFactory.java:6204)
at com.ibm.msg.client.jms.admin.JmsConnectionFactoryImpl.createConnection(JmsConnectionFactoryImpl.java:278)
at com.ibm.mq.jms.MQConnectionFactory.createCommonConnection(MQConnectionFactory.java:6155)
at com.ibm.mq.jms.MQQueueConnectionFactory.createQueueConnection(MQQueueConnectionFactory.java:115)
at com.ibm.mq.jms.MQQueueConnectionFactory.createConnection(MQQueueConnectionFactory.java:198)
at hermes.impl.jms.ConnectionManagerSupport.createConnection(ConnectionManagerSupport.java:122)
at hermes.impl.jms.ConnectionManagerSupport.createConnection(ConnectionManagerSupport.java:92)
at hermes.impl.jms.ConnectionSharedManager.reconnect(ConnectionSharedManager.java:81)
at hermes.impl.jms.ConnectionSharedManager.connect(ConnectionSharedManager.java:91)
at hermes.impl.jms.ConnectionSharedManager.getConnection(ConnectionSharedManager.java:104)
at hermes.impl.jms.ConnectionSharedManager.getObject(ConnectionSharedManager.java:142)
at hermes.impl.jms.ThreadLocalSessionManager.connect(ThreadLocalSessionManager.java:190)
at hermes.impl.jms.ThreadLocalSessionManager.getSession(ThreadLocalSessionManager.java:570)
at hermes.impl.jms.AbstractSessionManager.getDestination(AbstractSessionManager.java:460)

at hermes.impl.DefaultHermesImpl.getDestination(DefaultHermesImpl.java:367)
at hermes.browser.tasks.BrowseDestinationTask.invoke(BrowseDestinationTask.java:141)
at hermes.browser.tasks.TaskSupport.run(TaskSupport.java:175)
at hermes.browser.tasks.ThreadPool.run(ThreadPool.java:170)
at java.lang.Thread.run(Thread.java:619)
Caused by: com.ibm.mq.jmqi.JmqiException: CC=2;RC=2059;AMQ9204: Connection to host '127.0.0.1(1418)' rejected. [1=com.ibm.mq.jmqi.JmqiException[CC=2;RC=2059;AMQ9643: Remote SSL peer name error for channel 'qm5_ch3_ma'. [3=qm5_ch3_ma]],3=127.0.0.1(1418),5=RemoteConnection.analyseErrorSegment]
at com.ibm.mq.jmqi.remote.internal.RemoteFAP.jmqiConnect(RemoteFAP.java:1809)
at com.ibm.msg.client.wmq.internal.WMQConnection.<init>(WMQConnection.java:336)
... 20 more
Caused by: com.ibm.mq.jmqi.JmqiException: CC=2;RC=2059;AMQ9643: Remote SSL peer name error for channel 'qm5_ch3_ma'. [3=qm5_ch3_ma]
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnection.analyseErrorSegment(RemoteConnection.java:4223)
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnection.receiveTSH(RemoteConnection.java:2822)
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnection.initSess(RemoteConnection.java:1399)
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnection.connect(RemoteConnection.java:1078)
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnectionPool.getConnection(RemoteConnectionPool.java:338)
at com.ibm.mq.jmqi.remote.internal.RemoteFAP.jmqiConnect(RemoteFAP.java:1488)
... 21 more

Adjust SSLPeer to be the same as the client cert’s DN name – this should allow Hermes to be successful authenticated with MA, plus DN validation.
Test result with MA and DN lock-down on the MQ Server side.
Also Hermes as a JMS client can request MQ Cert’s DN for
SSLPeer validation. That’s Q Client can check the MQ server SSL Cert’ DN name. Below is the MQ Server cert labled: ibmwebspheremq<QMGR> ie.” ibmwebspheremqqm5” with CN = qm5


Hermes will need to setup SSLPeer (MQ server’s cert) to check for “cn=qm5”
SSLCipherSuite SSL_RSA_WITH_3DES_EDE_CBC_SHAchannel qm5_ch3_mahostName 127.0.0.1port 1418queueManager QM5transportType 1SSLPeerName cn=qm5

Try the “cn=qm5-bad-PEERNAME”
com.ibm.mq.MQException: JMSCMQ0001: WebSphere MQ call failed with compcode '2' ('MQCC_FAILED') reason '2398' ('MQRC_SSL_PEER_NAME_MISMATCH').Caused by: com.ibm.mq.jmqi.JmqiException: CC=2;RC=2398;AMQ9204: Connection to host '127.0.0.1(1418)' rejected. [1=com.ibm.mq.jmqi.JmqiException[CC=2;RC=2398;AMQ9636: SSL distinguished name does not match peer name, channel '?'. [4=CN=qm5, C=US]],3=127.0.0.1(1418),5=RemoteTCPConnection.protocolConnect]
Caused by: com.ibm.mq.jmqi.JmqiException: CC=2;RC=2398;AMQ9636: SSL distinguished name does not match peer name, channel '?'. [4=CN=qm5, C=US]

jre\lib\security\cacerts -listing.
C:\Program Files (x86)\Java\jdk1.6.0_13\bin> keytool -list -v -keystore ..\jre\lib\security\cacerts
Enter keystore password:
Keystore type: JKS
Keystore provider: SUN
Your keystore contains 72 entries
digicertassuredidrootca, 08/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): 87:CE:0B:7B:2A:0E:49:00:E1:58:71:9B:37:A8:93:72
trustcenterclass2caii, 08/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): CE:78:33:5C:59:78:01:6E:18:EA:B9:36:A0:B9:2E:23
thawtepremiumserverca, 13/02/1999, trustedCertEntry,
Certificate fingerprint (MD5): 06:9F:69:79:16:66:90:02:1B:8C:8C:A2:C3:07:6F:3A
swisssignsilverg2ca, 14/08/2008, trustedCertEntry,
Certificate fingerprint (MD5): E0:06:A1:C9:7D:CF:C9:FC:0D:C0:56:75:96:D8:62:13
swisssignplatinumg2ca, 14/08/2008, trustedCertEntry,
Certificate fingerprint (MD5): C9:98:27:77:28:1E:3D:0E:15:3C:84:00:B8:85:03:E6
equifaxsecureebusinessca2, 19/07/2003, trustedCertEntry,
Certificate fingerprint (MD5): AA:BF:BF:64:97:DA:98:1D:6F:C6:08:3A:95:70:33:CA
equifaxsecureebusinessca1, 19/07/2003, trustedCertEntry,
Certificate fingerprint (MD5): 64:9C:EF:2E:44:FC:C6:8F:52:07:D0:51:73:8F:CB:3D
thawteserverca, 13/02/1999, trustedCertEntry,
Certificate fingerprint (MD5): C5:70:C4:A2:ED:53:78:0C:C8:10:53:81:64:CB:D0:1D
entrustglobalclientca, 10/01/2003, trustedCertEntry,
Certificate fingerprint (MD5): 9A:77:19:18:ED:96:CF:DF:1B:B7:0E:F5:8D:B9:88:2E

utnuserfirstclientauthemailca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): D7:34:3D:EF:1D:27:09:28:E1:31:02:5B:13:2B:DD:F7
thawtepersonalfreemailca, 13/02/1999, trustedCertEntry,
Certificate fingerprint (MD5): 1E:74:C3:86:3C:0C:35:C5:3E:C2:7F:EF:3C:AA:3C:D9
utnuserfirsthardwareca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): 4C:56:41:E5:0D:BB:2B:E8:CA:A3:ED:18:08:AD:43:39
certumca, 11/02/2009, trustedCertEntry,
Certificate fingerprint (MD5): 2C:8F:9F:66:1D:18:90:B1:47:26:9D:8E:86:82:8C:A9
addtrustclass1ca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): 1E:42:95:02:33:92:6B:B9:5F:C0:7F:DA:D6:B2:4B:FC
equifaxsecureca, 19/07/2003, trustedCertEntry,
Certificate fingerprint (MD5): 67:CB:9D:C0:13:24:8A:82:9B:B2:17:1E:D1:1B:EC:D4
digicerthighassuranceevrootca, 08/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): D4:74:DE:57:5C:39:B2:D3:9C:85:83:C5:C0:65:49:8A
secomvalicertclass1ca, 02/05/2008, trustedCertEntry,
Certificate fingerprint (MD5): 65:58:AB:15:AD:57:6C:1E:A8:A7:B5:69:AC:BF:FF:EB
equifaxsecureglobalebusinessca1, 19/07/2003, trustedCertEntry,
Certificate fingerprint (MD5): 8F:5D:77:06:27:C4:98:3C:5B:93:78:E7:D7:7D:9B:CC
verisignclass3ca, 28/10/2003, trustedCertEntry,
Certificate fingerprint (MD5): 10:FC:63:5D:F6:26:3E:0D:F3:25:BE:5F:79:CD:67:67
deutschetelekomrootca2, 07/11/2008, trustedCertEntry,
Certificate fingerprint (MD5): 74:01:4A:91:B1:08:C4:58:CE:47:CD:F0:DD:11:53:08
verisignclass2ca, 28/10/2003, trustedCertEntry,
Certificate fingerprint (MD5): B3:9C:25:B1:C3:2E:32:53:80:15:30:9D:4D:02:77:3E
utnuserfirstobjectca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): A7:F2:E4:16:06:41:11:50:30:6B:9C:E3:B4:9C:B0:C9
thawtepersonalpremiumca, 13/02/1999, trustedCertEntry,

Certificate fingerprint (MD5): 3A:B2:DE:22:9A:20:93:49:F9:ED:C8:D2:8A:E7:68:0D
entrustgsslca, 10/01/2003, trustedCertEntry,
Certificate fingerprint (MD5): 9D:66:6A:CC:FF:D5:F5:43:B4:BF:8C:16:D1:2B:A8:99
verisignclass1ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): 97:60:E8:57:5F:D3:50:47:E5:43:0C:94:36:8A:B0:62
baltimorecodesigningca, 10/05/2002, trustedCertEntry,
Certificate fingerprint (MD5): 90:F5:28:49:56:D1:5D:2C:B0:53:D4:4B:EF:6F:90:22
baltimorecybertrustca, 10/05/2002, trustedCertEntry,
Certificate fingerprint (MD5): AC:B6:94:A5:9C:17:E0:D7:91:52:9B:B1:97:06:A6:E4
starfieldclass2ca, 21/01/2005, trustedCertEntry,
Certificate fingerprint (MD5): 32:4A:4B:BB:C8:63:69:9B:BE:74:9A:C6:DD:1D:46:24
qm5, 21/07/2012, trustedCertEntry,
Certificate fingerprint (MD5): 7A:2C:20:3A:CE:94:2B:44:F0:C4:65:C8:FD:A4:17:9F
camerfirmachamberscommerceca, 11/10/2008, trustedCertEntry,
Certificate fingerprint (MD5): B0:01:EE:14:D9:AF:29:18:94:76:8E:F1:69:33:2A:84
qm4, 21/07/2012, trustedCertEntry,
Certificate fingerprint (MD5): F0:32:DA:62:D7:4E:EF:28:04:5C:EA:B7:AA:06:10:E1
qm3, 21/07/2012, trustedCertEntry,
Certificate fingerprint (MD5): 1D:CA:FA:2F:0F:AD:01:0B:BD:8E:23:9B:39:FB:44:55
ttelesecglobalrootclass3ca, 11/02/2009, trustedCertEntry,
Certificate fingerprint (MD5): CA:FB:40:A8:4E:39:92:8A:1D:FE:8E:2F:C4:27:EA:EF
qm2, 21/07/2012, trustedCertEntry,
Certificate fingerprint (MD5): 9A:9F:EA:DC:8D:4B:73:74:09:08:60:3B:06:B4:7F:A2
qm1, 21/07/2012, trustedCertEntry,
Certificate fingerprint (MD5): 74:92:C7:FD:7E:0F:E4:08:3E:D9:8F:46:B1:4F:C0:E1
trustcenteruniversalcai, 08/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): 45:E1:A5:72:C5:A9:36:64:40:9E:F5:E4:58:84:67:8C

ttelesecglobalrootclass2ca, 11/02/2009, trustedCertEntry,
Certificate fingerprint (MD5): 2B:9B:9E:E4:7B:6C:1F:00:72:1A:CC:C1:77:79:DF:6A
verisignclass3g3ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): CD:68:B6:A7:C7:C4:CE:75:E0:1D:4F:57:44:61:92:09
certumtrustednetworkca, 11/02/2009, trustedCertEntry,
Certificate fingerprint (MD5): D5:E9:81:40:C5:18:69:FC:46:2C:89:75:62:0F:AA:78
verisignclass3g2ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): A2:33:9B:4C:74:78:73:D4:6C:E7:C1:F3:8D:CB:5C:E9
utndatacorpsgcca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): B3:A5:3E:77:21:6D:AC:4A:C0:C9:FB:D5:41:3D:CA:06
secomscrootca1, 02/05/2008, trustedCertEntry,
Certificate fingerprint (MD5): F1:BC:63:6A:54:E0:B5:27:F5:CD:E7:1A:E3:4D:6E:4A
gtecybertrustglobalca, 10/05/2002, trustedCertEntry,
Certificate fingerprint (MD5): CA:3D:D3:68:F1:03:5C:D0:32:FA:B8:2B:59:E8:5A:DB
trustcenterclass4caii, 08/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): 9D:FB:F9:AC:ED:89:33:22:F4:28:48:83:25:23:5B:E0
globalsignr2ca, 02/08/2007, trustedCertEntry,
Certificate fingerprint (MD5): 94:14:77:7E:3E:5E:FD:8F:30:BD:41:B0:CF:E7:D0:30
entrustclientca, 10/01/2003, trustedCertEntry,
Certificate fingerprint (MD5): 0C:41:2F:13:5B:A0:54:F5:96:66:2D:7E:CD:0E:03:F4
digicertglobalrootca, 08/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): 79:E4:A9:84:0D:7D:3A:96:D7:C0:4F:E2:43:4C:89:2E
globalsignca, 27/03/2008, trustedCertEntry,
Certificate fingerprint (MD5): 3E:45:52:15:09:51:92:E1:B7:5D:37:9F:B1:87:29:8A
geotrustglobalca, 19/07/2003, trustedCertEntry,
Certificate fingerprint (MD5): F7:75:AB:29:FB:51:4E:B7:77:5E:FF:05:3C:99:8E:F5
soneraclass2ca, 29/03/2006, trustedCertEntry,

Certificate fingerprint (MD5): A3:EC:75:0F:2E:88:DF:FA:48:01:4E:0B:5C:48:6F:FB
verisigntsaca, 14/08/2008, trustedCertEntry,
Certificate fingerprint (MD5): 7F:66:7A:71:D3:EB:69:78:20:9A:51:14:9D:83:DA:20
soneraclass1ca, 29/03/2006, trustedCertEntry,
Certificate fingerprint (MD5): 33:B7:84:F5:5F:27:D7:68:27:DE:14:DE:12:2A:ED:6F
valicertclass2ca, 21/01/2005, trustedCertEntry,
Certificate fingerprint (MD5): A9:23:75:9B:BA:49:36:6E:31:C2:DB:F2:E7:66:BA:87
comodoaaaca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): 49:79:04:B0:EB:87:19:AC:47:B0:BC:11:51:9B:74:D0
aolrootca2, 27/03/2008, trustedCertEntry,
Certificate fingerprint (MD5): D6:ED:3C:CA:E2:66:0F:AF:10:43:0D:77:9B:04:09:BF
addtrustqualifiedca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): 27:EC:39:47:CD:DA:5A:AF:E2:9A:01:65:21:A9:4C:BB
aolrootca1, 18/01/2008, trustedCertEntry,
Certificate fingerprint (MD5): 14:F1:08:AD:9D:FA:64:E2:89:E7:1C:CF:A8:AD:7D:5E
verisignclass2g3ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): F8:BE:C4:63:22:C9:A8:46:74:8B:B8:1D:1E:4A:2B:F6
addtrustexternalca, 02/05/2006, trustedCertEntry,
Certificate fingerprint (MD5): 1D:35:54:04:85:78:B0:3F:42:42:4D:BF:20:73:0A:3F
verisignclass2g2ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): 2D:BB:E5:25:D3:D1:65:82:3A:B7:0E:FA:E6:EB:E2:E1
swisssigngoldg2ca, 14/08/2008, trustedCertEntry,
Certificate fingerprint (MD5): 24:77:D9:A8:91:D1:3B:FA:88:2D:C2:FF:F8:CD:33:93
entrust2048ca, 10/01/2003, trustedCertEntry,
Certificate fingerprint (MD5): BA:21:EA:20:D6:DD:DB:8F:C1:57:8B:40:AD:A1:FC:FC
gtecybertrust5ca, 10/05/2002, trustedCertEntry,
Certificate fingerprint (MD5): 7D:6C:86:E4:FC:4D:D1:0B:00:BA:22:BB:4E:7C:6A:8E

camerfirmachambersignca, 11/10/2008, trustedCertEntry,
Certificate fingerprint (MD5): 9E:80:FF:78:01:0C:2E:C1:36:BD:FE:96:90:6E:08:F3
verisignserverca, 30/06/1998, trustedCertEntry,
Certificate fingerprint (MD5): 74:7B:82:03:43:F0:00:9E:6B:B3:EC:47:BF:85:A5:93
camerfirmachambersca, 11/10/2008, trustedCertEntry,
Certificate fingerprint (MD5): 5E:80:9E:84:5A:0E:65:0B:17:02:F3:55:18:2A:3E:D7
entrustsslca, 10/01/2003, trustedCertEntry,
Certificate fingerprint (MD5): DF:F2:80:73:CC:F1:E6:61:73:FC:F5:42:E9:C5:7C:EE
godaddyclass2ca, 21/01/2005, trustedCertEntry,
Certificate fingerprint (MD5): 91:DE:06:25:AB:DA:FD:32:17:0C:BB:25:17:2A:84:67
verisignclass1g3ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): B1:47:BC:18:57:D1:18:A0:78:2D:EC:71:E8:2A:95:73
secomevrootca1, 02/05/2008, trustedCertEntry,
Certificate fingerprint (MD5): 22:2D:A6:01:EA:7C:0A:F7:F0:6C:56:43:3F:77:76:D3
thawtepersonalbasicca, 13/02/1999, trustedCertEntry,
Certificate fingerprint (MD5): E6:0B:D2:C9:CA:2D:88:DB:1A:71:0E:4B:78:EB:02:41
verisignclass1g2ca, 26/03/2004, trustedCertEntry,
Certificate fingerprint (MD5): DB:23:3D:F9:69:FA:4B:B9:95:80:44:73:5E:7D:41:83
C:\Program Files (x86)\Java\jdk1.6.0_13\bin>

com.ibm.mq.MQException: JMSCMQ0001: WebSphere MQ call failed with compcode '2' ('MQCC_FAILED') reason '2397' ('MQRC_JSSE_ERROR').
at com.ibm.msg.client.wmq.common.internal.Reason.createException(Reason.java:223)
at com.ibm.msg.client.wmq.internal.WMQConnection.<init>(WMQConnection.java:421)
at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createV7ProviderConnection(WMQConnectionFactory.java:6807)
at com.ibm.msg.client.wmq.factories.WMQConnectionFactory.createProviderConnection(WMQConnectionFactory.java:6204)
at com.ibm.msg.client.jms.admin.JmsConnectionFactoryImpl.createConnection(JmsConnectionFactoryImpl.java:278)
at com.ibm.mq.jms.MQConnectionFactory.createCommonConnection(MQConnectionFactory.java:6155)
at com.ibm.mq.jms.MQQueueConnectionFactory.createQueueConnection(MQQueueConnectionFactory.java:115)
at com.ibm.mq.jms.MQQueueConnectionFactory.createConnection(MQQueueConnectionFactory.java:198)
at hermes.impl.jms.ConnectionManagerSupport.createConnection(ConnectionManagerSupport.java:122)
at hermes.impl.jms.ConnectionManagerSupport.createConnection(ConnectionManagerSupport.java:92)
at hermes.impl.jms.ConnectionSharedManager.reconnect(ConnectionSharedManager.java:81)
at hermes.impl.jms.ConnectionSharedManager.connect(ConnectionSharedManager.java:91)
at hermes.impl.jms.ConnectionSharedManager.getConnection(ConnectionSharedManager.java:104)

at hermes.impl.jms.ConnectionSharedManager.getObject(ConnectionSharedManager.java:142)
at hermes.impl.jms.ThreadLocalSessionManager.connect(ThreadLocalSessionManager.java:190)
at hermes.impl.jms.ThreadLocalSessionManager.getSession(ThreadLocalSessionManager.java:570)
at hermes.impl.jms.AbstractSessionManager.getDestination(AbstractSessionManager.java:460)
at hermes.impl.DefaultHermesImpl.getDestination(DefaultHermesImpl.java:367)
at hermes.browser.tasks.BrowseDestinationTask.invoke(BrowseDestinationTask.java:141)
at hermes.browser.tasks.TaskSupport.run(TaskSupport.java:175)
at hermes.browser.tasks.ThreadPool.run(ThreadPool.java:170)
at java.lang.Thread.run(Thread.java:619)
Caused by: com.ibm.mq.jmqi.JmqiException: CC=2;RC=2397;AMQ9204: Connection to host '127.0.0.1(1418)' rejected. [1=com.ibm.mq.jmqi.JmqiException[CC=2;RC=2397;AMQ9771: SSL handshake failed. [1=java.net.SocketException[java.security.NoSuchAlgorithmException: Error constructing implementation (algorithm: Default, provider: SunJSSE, class: com.sun.net.ssl.internal.ssl.DefaultSSLContextImpl)],3=Seri-THINK/127.0.0.1:1418 (Seri-THINK),4=SSLSocket.createSocket,5=default]],3=127.0.0.1(1418),5=RemoteTCPConnection.makeSocketSecure]
at com.ibm.mq.jmqi.remote.internal.RemoteFAP.jmqiConnect(RemoteFAP.java:1809)
at com.ibm.msg.client.wmq.internal.WMQConnection.<init>(WMQConnection.java:336)
... 20 more
Caused by: com.ibm.mq.jmqi.JmqiException: CC=2;RC=2397;AMQ9771: SSL handshake failed. [1=java.net.SocketException[java.security.NoSuchAlgorithmException: Error constructing implementation (algorithm: Default, provider: SunJSSE, class: com.sun.net.ssl.internal.ssl.DefaultSSLContextImpl)],3=Seri-THINK/127.0.0.1:1418 (Seri-THINK),4=SSLSocket.createSocket,5=default]
at com.ibm.mq.jmqi.remote.internal.RemoteTCPConnection.makeSocketSecure(RemoteTCPConnection.java:1621)
at com.ibm.mq.jmqi.remote.internal.RemoteTCPConnection.connnectUsingLocalAddress(RemoteTCPConnection.java:618)

at com.ibm.mq.jmqi.remote.internal.RemoteTCPConnection.protocolConnect(RemoteTCPConnection.java:935)
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnection.connect(RemoteConnection.java:1075)
at com.ibm.mq.jmqi.remote.internal.system.RemoteConnectionPool.getConnection(RemoteConnectionPool.java:338)
at com.ibm.mq.jmqi.remote.internal.RemoteFAP.jmqiConnect(RemoteFAP.java:1488)
... 21 more
Caused by: java.net.SocketException: java.security.NoSuchAlgorithmException: Error constructing implementation (algorithm: Default, provider: SunJSSE, class: com.sun.net.ssl.internal.ssl.DefaultSSLContextImpl)
at javax.net.ssl.DefaultSSLSocketFactory.throwException(SSLSocketFactory.java:179)
at javax.net.ssl.DefaultSSLSocketFactory.createSocket(SSLSocketFactory.java:199)
at com.ibm.mq.jmqi.remote.internal.RemoteTCPConnection.makeSocketSecure(RemoteTCPConnection.java:1614)
... 26 more
Caused by: java.security.NoSuchAlgorithmException: Error constructing implementation (algorithm: Default, provider: SunJSSE, class: com.sun.net.ssl.internal.ssl.DefaultSSLContextImpl)
at java.security.Provider$Service.newInstance(Provider.java:1245)
at sun.security.jca.GetInstance.getInstance(GetInstance.java:220)
at sun.security.jca.GetInstance.getInstance(GetInstance.java:147)
at javax.net.ssl.SSLContext.getInstance(SSLContext.java:125)
at javax.net.ssl.SSLContext.getDefault(SSLContext.java:68)
at javax.net.ssl.SSLSocketFactory.getDefault(SSLSocketFactory.java:102)
at com.ibm.mq.jmqi.remote.internal.RemoteTCPConnection.chooseSocketFactory(RemoteTCPConnection.java:2073)

at com.ibm.mq.jmqi.remote.internal.RemoteTCPConnection.makeSocketSecure(RemoteTCPConnection.java:1604)
... 26 more
Caused by: java.security.NoSuchProviderException: no such provider: sun.security.provider.Sun11
at sun.security.jca.GetInstance.getService(GetInstance.java:66)
at sun.security.jca.GetInstance.getInstance(GetInstance.java:190)
at java.security.Security.getImpl(Security.java:662)
at java.security.KeyStore.getInstance(KeyStore.java:632)
at com.sun.net.ssl.internal.ssl.DefaultSSLContextImpl.getDefaultKeyManager(DefaultSSLContextImpl.java:145)
at com.sun.net.ssl.internal.ssl.DefaultSSLContextImpl.<init>(DefaultSSLContextImpl.java:40)
at sun.reflect.NativeConstructorAccessorImpl.newInstance0(Native Method)
at sun.reflect.NativeConstructorAccessorImpl.newInstance(NativeConstructorAccessorImpl.java:39)
at sun.reflect.DelegatingConstructorAccessorImpl.newInstance(DelegatingConstructorAccessorImpl.java:27)
at java.lang.reflect.Constructor.newInstance(Constructor.java:513)
at java.lang.Class.newInstance0(Class.java:355)
at java.lang.Class.newInstance(Class.java:308)
at java.security.Provider$Service.newInstance(Provider.java:1221)
... 33 more
Related Documents