-
8/10/2019 Disc Her
1/47
2010 LearnMikroTik.com 1
Port Knocking for Security
-
8/10/2019 Disc Her
2/47
2010 LearnMikroTik.com 2
Introduction
Steve Discher - LearnMikroTik.com
MikroTik RouterOS training, includingMTCNA, MTCRE, MTCTCE, MTCWE andMTCUME
Own a WISP
-
8/10/2019 Disc Her
3/47
2010 LearnMikroTik.com 3
Introduction
Just completed a 10,000 mile, 100 day journey around western USA teachingRouterOS, the MikroTik Road Show
-
8/10/2019 Disc Her
4/47
2010 LearnMikroTik.com 4
The Road Show was a 100 day journeythat started in College Station, Texas inApril
Purpose was to travel all over the westernUS conducting MikroTik RouterOS trainingin as many locations as possible
-
8/10/2019 Disc Her
5/47
2010 LearnMikroTik.com 5
Road Show StatsMiles Traveled: 10,000 by motor home
3,000 by JeepFuel Used: 1,111 gals of Diesel
Nights on the road: 100
Areas Traveled: 11 US states, 3 islands and 2
Canadian Provinces
-
8/10/2019 Disc Her
6/47
2010 LearnMikroTik.com 6
Road Show StatsTrainings Conducted: 5 public, 6 private, consulted with 9different companies
MT Certifications Issued: 35
Look for the next MikroTik Road Show, Summer 2011
www.MTRoadShow.com
-
8/10/2019 Disc Her
7/47
2010 LearnMikroTik.com 7
Port Knocking for Security
-
8/10/2019 Disc Her
8/47
2010 LearnMikroTik.com 8
What is Port Knocking? Port knocking is a method of externally
opening ports on a firewall by generating aconnection attempt on a set of pre-specified series of closed ports
-
8/10/2019 Disc Her
9/47
2010 LearnMikroTik.com 9
What is Port Knocking? The port "knock" itself is similar to a secret
handshake and can consist of any numberof TCP, UDP, or ICMP or other protocolpackets to numbered ports on thedestination machine
-
8/10/2019 Disc Her
10/47
2010 LearnMikroTik.com 10
What is Port Knocking? The knock may also consist of text strings
sent to the device being knocked to addadditional complexity and security
-
8/10/2019 Disc Her
11/47
2010 LearnMikroTik.com 11
Port Knocking Example
Knocking PortPORT 1234PORT 4321
1. Send a connection to PORT-1234
2. The router stores therequesters IP for an amountof time
3. Send a connection to PORT-4321
4. The router checks to see if the IPis the same IP from the firstconnection (PORT-1234)
5. If the IP is the same and the timebetween 1 st attempt and 2 nd iswithin a specified time then the
requester IP will be allowed toaccess the router
-
8/10/2019 Disc Her
12/47
2010 LearnMikroTik.com 12
Firewall Chain Review
-
8/10/2019 Disc Her
13/47
2010 LearnMikroTik.com 13
Input Chain Input Chain used to process packets
entering the router through one of theinterfaces with the destination IP addresswhich is one of the router's addresses.Packets passing through the router are notprocessed against the rules of the input
chain. Protects the router itself.
-
8/10/2019 Disc Her
14/47
2010 LearnMikroTik.com 14
Forward Chain Forward Chain - used to process packets
passing through the router. Protects theclients.
-
8/10/2019 Disc Her
15/47
2010 LearnMikroTik.com 15
Output Chain Output Chain used to process packets
generated by the router. Packets passingthrough the router are not processedagainst the rules of the output chain.
-
8/10/2019 Disc Her
16/47
2010 LearnMikroTik.com 16
Port Knocking Strategy1. Detect a connection to a port and put it in
an address list we will name temporaryfor 10 seconds.
2. Detect a connection to a second port andcheck to see if the source IP is in theaddress list temporary. If so, put in the
list secured.3. Allow access to the router from hosts in
the address list secured.
-
8/10/2019 Disc Her
17/47
2010 LearnMikroTik.com 17
Port Knocking Strategy
Host12.10.1.3
PORT1234
Host12.10.1.3
PORT1234
Router
Create AddressList Entrytemporary
12.10.1.3 for 10secs
Create AddressList Entry
temporary12.10.1.3 for 10
secs
Host12.10.1.3
PORT4321
Host12.10.1.3
PORT4321
FW Rule: If
12.10.1.3is in temporary,add to secured
FW Rule: If
12.10.1.3is in temporary,add to secured
First
Second
-
8/10/2019 Disc Her
18/47
2010 LearnMikroTik.com 18
Address Lists If you have not used Address Lists in
RouterOS before, you are missing a greatway to reduce the number of rules in yourfirewall and create a much moreextensible firewall device
Lets take a look at Address Lists
-
8/10/2019 Disc Her
19/47
2010 LearnMikroTik.com 19
Address Lists
-
8/10/2019 Disc Her
20/47
2010 LearnMikroTik.com 20
Address Lists
-
8/10/2019 Disc Her
21/47
2010 LearnMikroTik.com 21
Address Lists
-
8/10/2019 Disc Her
22/47
2010 LearnMikroTik.com 22
Address Lists
-
8/10/2019 Disc Her
23/47
2010 LearnMikroTik.com 23
Port Knocking Strategy1. Detect a connection to a port and put in
an address list entry temporary for 10seconds.
2. Detect a connection to a second port andcheck to see if the source IP is in theaddress list temporary. If so, put in the
list secured.3. Allow access to the router from hosts in
the address list secured.
-
8/10/2019 Disc Her
24/47
2010 LearnMikroTik.com 24
Configuration Step 1
-
8/10/2019 Disc Her
25/47
2010 LearnMikroTik.com 25
Configuration Step 1
-
8/10/2019 Disc Her
26/47
2010 LearnMikroTik.com 26
Configuration Step 1
Spectrum indonesia 26
Trap TCP(1234) and put the source address
to address-list temporary for 10 seconds
-
8/10/2019 Disc Her
27/47
2010 LearnMikroTik.com 27
Configuration Step 2Trap TCP(4321) and src-address is in temporary. Put itto address-list secured
-
8/10/2019 Disc Her
28/47
2010 LearnMikroTik.com 28
Configuration Step 3Allow access from src-address-list
secured
-
8/10/2019 Disc Her
29/47
2010 LearnMikroTik.com 29
Configuration Step 4Drop everything else
-
8/10/2019 Disc Her
30/47
2010 LearnMikroTik.com 30
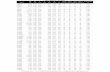
Configuration Summary
-
8/10/2019 Disc Her
31/47
2010 LearnMikroTik.com 31
Generating The KnockTo generate the knock you need a client. There
are numerous clients for download for Windows,Linux or Mac.
Knock.exehttp://www.zeroflux.org/proj/knock/files/knock-cygwin.zip
Or, build your own!
-
8/10/2019 Disc Her
32/47
2010 LearnMikroTik.com 32
Generating The Knock
-
8/10/2019 Disc Her
33/47
2010 LearnMikroTik.com 33
Knock Is Complete!
-
8/10/2019 Disc Her
34/47
2010 LearnMikroTik.com 34
Whats The Effectiveness? Because any combination of ports and transport
protocols can be used, the number of possiblesequences that an attacker would have to guessis very high. Even if the hacker knew only two
port knocks were involved, as in the very simpleexample above, with 64,000 possible TCP, UDP,and ICMP ports to choose from, the resulting set
of possible combinations for the hacker to tryruns into the millions.
-
8/10/2019 Disc Her
35/47
2010 LearnMikroTik.com 35
Whats The Effectiveness? Port scanners will be frustrated because
port knocking uses closed ports to do thelistening.
-
8/10/2019 Disc Her
36/47
2010 LearnMikroTik.com 36
Whats The Effectiveness? The biggest advantage of all is that port
knocking is platform-, service-, andapplication-independent: Any OS with thecorrect client and server software can takeadvantage of its protection
-
8/10/2019 Disc Her
37/47
2010 LearnMikroTik.com 37
Whats The Effectiveness? Port knocking can also serve as an extra
layer of security to protect high-risk remotemanagement services, such as SSH andRDP.
-
8/10/2019 Disc Her
38/47
2010 LearnMikroTik.com 38
Whats The Effectiveness? Critics often point to the fact that
eavesdropping hackers might be able tocapture and replay the successful port-knocking sequence or series of bytes.True, but port knocking should be just alayer on top of other types of security such
as tunnels, or allowed IP addresses.
-
8/10/2019 Disc Her
39/47
2010 LearnMikroTik.com 39
Whats The Effectiveness? If a hacker does manage to glean your
combination, the worst-case scenario isthat the intruder bypasses the port-knocking protection and now has to faceyour normal service security measures.
-
8/10/2019 Disc Her
40/47
2010 LearnMikroTik.com 40
Some Ideas Use port knocking to augment existing
security such as VPN tunnels. Forexample, client must knock before youallow VPN connection.
Extend port knocking to include sendingtext passphrases. Client must knock
correct ports, correct protocol, correctsequence and send the right string duringthe sequence.
-
8/10/2019 Disc Her
41/47
2010 LearnMikroTik.com 41
Extending Knock - Example Using Autoit ( www.autoitscript.com ),
create an application to send text stringsto udp ports in sequence Use Layer 7 rules to watch for strings sent
to certain ports Based my firewall filter rules on Layer 7
rules
-
8/10/2019 Disc Her
42/47
2010 LearnMikroTik.com 42
Create Knock Client App Step 1 Autoit script:
U DPStartup()
$socket = UDP Open("10.0.1.1", 1234)
$status = UDPSend($socket, "supersecretpassword1")UDPCloseSocket($socket)
$socket = UDP Open("10.0.1.1", 4321)
$status = UDPSend($socket, "supersecretpassword2")
UDPCloseSocket($socket)
UDPShutdown()
-
8/10/2019 Disc Her
43/47
2010 LearnMikroTik.com 43
Create Layer 7 Rules Step 2/ipfirewall layer7-protocol
add comment="" na me=knock1regexp="supersecretpassword1\$"
add comment="" na me=knock2
regexp="supersecretpassword2\$"
-
8/10/2019 Disc Her
44/47
2010 LearnMikroTik.com 44
Create Firewall Rules Step 3/ipfirewall filter
add action=add-src-to-address-list address-list=temporary \
address-list-timeout=10s chain=input comment="" disabled=no dst-port=1234 \
layer7-protocol=knock1 protocol=udp
add action=add-src-to-address-list address-list=secured address-list-timeout=\
10s chain=input com ment="" disabled=no dst-port=4321 layer7-protocol=\
knock2 protocol=udp src-address-list=temporary
add action=accept chain=input com ment="" disabled=no src-address-list=secured
add action=drop chain=input com ment="" disabled=no
-
8/10/2019 Disc Her
45/47
2010 LearnMikroTik.com 45
Demonstration
-
8/10/2019 Disc Her
46/47
2010 LearnMikroTik.com 46
Questions?
-
8/10/2019 Disc Her
47/47
2010 LearnMikroTik.com 47
Thank You
LearnMikroTik.comhttp://www.LearnMikroTik.com