1 © 2003 Cisco Systems, Inc. All rights reserved. Presentation_ID ETHICAL HACKING

Welcome message from author
This document is posted to help you gain knowledge. Please leave a comment to let me know what you think about it! Share it to your friends and learn new things together.
Transcript
222© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Introduction to Hacking
Hacker
Hacking
Cracker
Ethical Hacker
333© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Types of Hackers
• WHITE HATS ( aka Ethical hackers)
• BLACK HATS
• GREY HATS
444© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Purpose of Hacking
• To make security stronger(Ethical Hacking )
• Just for fun
• Show off
• Steal important information
• Destroy enemy’s computer network
555© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking
• “Ethical hacking describes the process of attacking and penetrating computer systems and networks to discover and point out potential security weaknesses for a client .”
• Its Legal and Permission is obtained from the target for hacking.
• Part of an overall security program
666© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking Terminology
• Exploit
• Vulnerability
• Target of Evaluation (TOE)
777© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacker’s purpose
Ethical hackers try to answer:
What can the intruder see on the target system?
What can an intruder do with that information?
Does anyone at the target notice the intruders attempts or success?
The main process of Ethical Hacking is testing the security of a system or network known as a penetration test, or pen test.
888© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Types of Ethical Hackers
Black Box Penetration Testers
White Box Penetration Testers
Certified Ethical Hacker/Licensed Penetration Tester
999© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Penetration Test
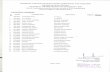
Figure : Phases of penetration testing
• Testing the security of a system or network is known as a penetration test, or pen test.
111111© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking process-Reconnaissance
A. Understanding Competitive Intelligence
B. Footprinting
Footprinting is defined as the process of creating a blueprint or map of an organization’s network and systems. Footprinting includes:
121212© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
• Domain name
• Network services and applications
• System architecture
• Authentication mechanisms
• IP address ranges
• Access control mechanisms
• Phone numbers
• Contact addresses
Tools – whois, Traceroute VisualRoute, and NeoTrace,
131313© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking process-Scanning
• Scanning is the process of locating systems that are alive and responding on the network.
Scanning type Purpose
Port scanning Determine open ports and services.
Network scanning Determine active hosts and their IP addresses on a given network or subnet.
Vulnerability scanning Identifies the operating system , version number, service packs and vulnerabilities in the operating system.
141414© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking process-Scanning
Tools:-
• port scanning(nscan,nmap,Hping2,Superscan),
• Network scanning(nscan,nacrosoft traceroute, tcpdump, nmap, strobe, rprobe,Nessus, Cybercop,FireWalk)
• vulnerability scanning( NetScanTools Pro, Nessus, Nikto, Core impact, Retina, etc. and www.milw0rm.com and http://www.packetstormsecurity.org/)
151515© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking process-Gaining Access
Gaining access is known in the hacker world as owning the system because once a system has been hacked, the hacker has control and can use that system as they wish.
• A. Cracking a Password
• B. Keyloggers
• C . Banner Grabbing
161616© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking process-Maintaining Access
• keyloggers
• Rootkits
Effects
– Infect startup files
– Plant remote control services
– Install monitoring mechanisms
– Replace apps with trojans
171717© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking process-Clearing Tracks
• Avoid detection by security personnel
• To continue to use the owned system
• To remove evidence of hacking
• To avoid legal action.
Techniques
– Clear logs
– Hide log files
181818© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Ethical Hacking: Literature Survey
• Microsoft pays out $100,000 and $11,000 to a White hat hacker(James Forshaw).
• Adobe was hit by a massive security breach
• Brazil announces “U.S proof” secure email system to avoid spying
• Major Indian telecoms company “Hathway” websites hacked by Pakistani hackers
• Hacked Teen sold mom’s jewelry after hackers threatened to share his Shameful footage
191919© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Some Techniques of Ethical Hacking
Spoofing attack (Phishing)
Trojan horses
SQL Injection
Vulnerability scanner
Key loggers
202020© 2003 Cisco Systems, Inc. All rights reserved.Presentation_ID
Some Famous Ethical Hackers
• James Forshaw
• Ankit Fadia
• Kevin Mitnick
• George Hotz
• Robert Morris
• Max Butler
• Kevin Poulsen
Related Documents