European pass conference 2008 - sql server development - security best practices - charley hanania
Dec 22, 2014
Welcome message from author
This document is posted to help you gain knowledge. Please leave a comment to let me know what you think about it! Share it to your friends and learn new things together.
Transcript


SECURITY BEST PRACTICESFor SQL Server Development
Charley HananiaB.Sc (Computing Science), MCP, MCDBA, MCITP, MCTS, MCT
Senior Database Specialist
Production Product Owner – MS SQL Server
UBS Investment Bank

3
Outline
•Why is Security important?•Reducing Attack Surface•Trustworthy Computing•The Principle of Least Privilege
D2-S5-AD – SQL Server Development: Security Best Practices

Authenticate and authorise
Reduce
surface
areaAudi
t even
tsEncrypt
Security Principles
D2-S5-AD – SQL Server Development: Security Best Practices

#
of C
VE
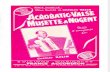
Notes: Updated as of 10/18/2007. Vulnerabilities are included for SQL Server 2000 , SQL Server 2005 . Oracle (8i, 9i, 9iR2, 10g, 10gR2)Query for Oracle was run with vendor name: ‘Oracle’ , and product name: ‘any’ (all database product name variations were queried) .Query for Microsoft was run with vendor name: ‘Microsoft ‘ ; product name: ‘Microsoft SQL Server’; version name: ’Any’
Source: NIST National Vulnerability Database
2002 2003 2004 2005 2006 20070
40
80
120
160
2002; SQL Server; 24
2003; SQL Server; 3
2004; SQL Server; 0
2005; SQL Server; 0
2006; SQL Server; 0
2007; SQL Server; 0
2002; Oracle Database; 46
2003; Oracle Database; 12
2004; Oracle Database; 25
2005; Oracle Database; 61
2006; Oracle Database; 144
2007; Oracle Database; 41
SQL Server Oracle Database
Is Security something that MS are focused on?
D2-S5-AD – SQL Server Development: Security Best Practices

Network
Operating System
DatabaseMgt System
ProtocolsPorts
SharesServices
Accounts
Auditing &Logging
Files &Directories
Registry
Patches &Updates
SQL SERVER SECURITY THROUGH PERMISSIONING
LOGIN
SUSE
RSAND
ROLES SCHEMAS
AND
OBJECTS
EXECUTION
CONTEXTS
ENCRYPTION
Firewalls
Packet Filters
Installed Features
Enabled Components
Authentication Modes
Endpoints
Defence in DepthUsing a layered Approach
D2-S5-AD – SQL Server Development: Security Best Practices

7
Demo
Context Switching
D2-S5-AD – SQL Server Development: Security Best Practices

Authorization
• Principle of Least Privileges• Rich Access Control Model
– Granular permissions– Choice of appropriate scope (database, schema,
object, sub-object)– Role Based Access control– Application module based
access control– Minimizing application impact for user management– Both Data (above) and Metadata
• Ease of security management
D2-S5-AD – SQL Server Development: Security Best Practices

9
Demo
Data Encryption within TablesEncrypting Sensitive Data
D2-S5-AD – SQL Server Development: Security Best Practices

Data Encryption• Why consider encryption?
– Additional layer of security– Required by some regulatory compliance
laws
• In SQL Server 2000– Vendor support required
• In SQL Server 2005– Built-in support for explicit data encryption
• In SQL Server 2008– Transparent data encryption– Extensible key management
ThreatDetected
EmergencyProcedure
Server HighlyProtected
D2-S5-AD – SQL Server Development: Security Best Practices

SQL Server Cryptographic Capabilities
• Transparent Data Encryption and Decryption built-in• DDL for creation of
– Symmetric Keys– Asymmetric Keys and Certificates
• Symmetric Keys and Private Keys are stored encrypted• Securing the Keys themselves
– Based on user passwords– Automatic, using SQL Server key management
D2-S5-AD – SQL Server Development: Security Best Practices

Encryption Algorithm Support
• Algorithms andkey lengths vary; depends on CSP (Cryptographic Services Provider)
• Performance depends on size of data being ciphered
XP SP2 WS2003
DES 56 (64) 56 (64)
3DES 128 128
DESX 184 184
AES128 - 128
AES192 - 192
AES256 - 256
RC2 128 128
RC4 40 40
RC4_128 128 128
RSA 2048 2048
D2-S5-AD – SQL Server Development: Security Best Practices

13
Demo
User Schema SeparationMoving objects into other schemas
D2-S5-AD – SQL Server Development: Security Best Practices

Sharepoint Integration
Transparent Data Encryption
External Key Management
Hot Pluggable CPU support
Data Auditing
Data Compression Backup Compression
Enhanced Database Mirroring
Performance Data Collection
Improved Plan Guide Support
Resource Governor
Improved Datatypes
HierarchyID
LinQChange Data Capture
Table Valued Parameters
Large UDTS
MERGE StatementsXML Enhancements
Service Broker EnhancementsSpatial DataPolicy based Management
Microsoft System Center Integration
Extended Events
Data Compression
FILESTREAM
Integrated Full Text Indexing
Sparse ColumnsNew Index Types
Partition Table Parallelism
Star Join Support
Persistent Lookups
Improved Thread Scheduling
MERGE Statement
Change Data Capture
Scale-out Analysis Services
Subspace Computations
Data Mining Add-ins for ExcelIIS Agnostic RS
Rich Text SupportReport Designer
Word/Excel Designing
Entity Data Model
So What’s New in SQL Server 2008?
D2-S5-AD – SQL Server Development: Security Best Practices

Transparent Data Encryption
• Encryption/decryption occurs at the database
– Uses Database Encryption Key (DEK)• Applications do not need to handle
encryption/decryption of data– Treat encrypted and unencrypted data in
an identical way• DEK is encrypted with:
– Password– Service Master Key– Hardware Security Module
• DEK must be decrypted to attach database files or restore a backup
SQL Server 2008
DEK
Client Application
Encrypted data page
D2-S5-AD – SQL Server Development: Security Best Practices

16
Links
•Hello Secure Worldhttp://www.microsoft.com/click/hellosecureworld/default.mspx
•Microsoft Security Assessment Tool http://www.microsoft.com/downloads/details.aspx?FamilyID=6D79DF9C-C6D1-4E8F-8000-0BE72B430212&displaylang=en
•Microsoft Application Verifierhttp://www.microsoft.com/downloads/details.aspx?FamilyID=bd02c19c-1250-433c-8c1b-2619bd93b3a2&DisplayLang=en
•Microsoft Threat Analysis & Modelling Toolhttp://www.microsoft.com/downloads/details.aspx?FamilyID=59888078-9daf-4e96-b7d1-944703479451&DisplayLang=en
•How To: Protect From SQL Injection in ASP.NEThttp://msdn2.microsoft.com/en-us/library/ms998271.aspx
•Securing Your Database Serverhttp://msdn.microsoft.com/en-us/library/aa302434.aspx
•Threats and Countermeasureshttp://www.microsoft.com/technet/security/guidance/serversecurity/tcg/tcgch00.mspx
D2-S5-AD – SQL Server Development: Security Best Practices

Questions?

Thank you!
Related Documents